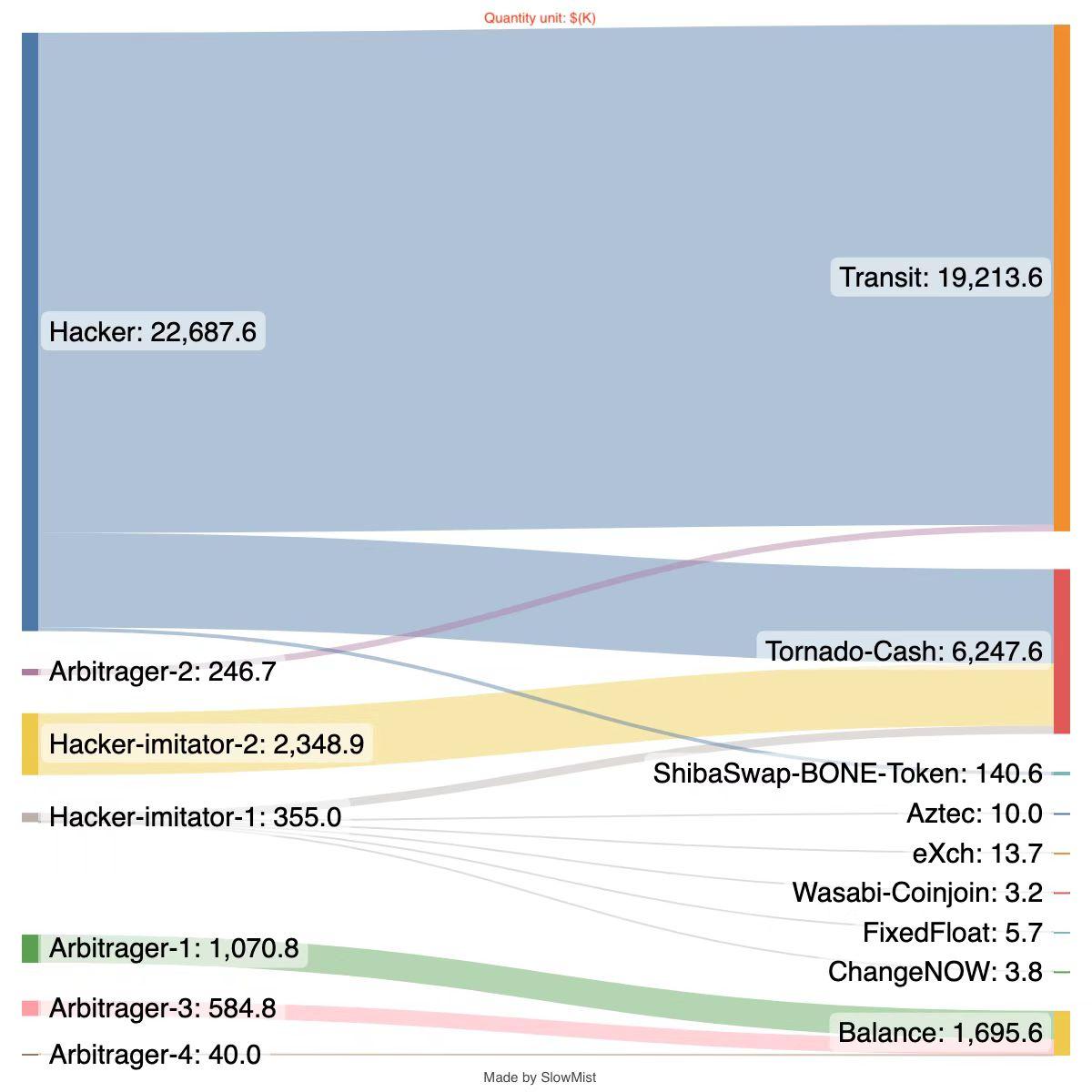
Slow Mist: More than $6 million in funds transferred to Tornado Cash during the Transit Swap event
Chain Catcher news, blockchain security agency Slow Mist's MistTrack has conducted a follow-up analysis on the fund transfers related to the Transit Swap incident, revealing that the attacker transferred over $6 million to Tornado Cash. The analysis is as follows:
Hacker#1 Attacker (the hacker who stole the largest amount), profit amount: approximately $24.1 million
1: 0x75F2…FFD46
2: 0xfa71…90fb
Has returned over $18.9 million of the stolen funds; deposited 12,500 BNB to Tornado Cash; transferred approximately 14 million MOONEY tokens and 67,709 DAI tokens to ShibaSwap: BONE Token contract address.
Hacker#2 Arbitrage Bot-1, profit amount: 1,166,882.07 BUSD
0xcfb0…7ac7(BSC)
Retained in the profit address, no further transfers.
Hacker#3 Attacker Imitator-1, profit amount: 356,690.71 USDT
0x87be…3c4c(BSC)
USDT exchanged across chains or multiple times for other tokens using tools like Synapse, PancakeSwap, and 1inch. Ultimately deposited 10,005.3 USDC to Aztec; 13,745.37 USDC to eXch; 0.2626 BTC mixed using Wasabi Coinjoin; 0.462 BTC deposited to FixedFloat; 3,797.94 BUSD deposited to ChangeNOW; 1,125.2 BNB deposited to Tornado Cash.
Hacker#4 Arbitrage Bot-2, profit amount: 246,757.31 USDT
0x0000…4922(BSC)
All funds have been recovered.
Hacker#5 Arbitrage Bot-3, profit amount: 584,801.17 USDC
0xcc3d…ae7d(BSC)
All USDC transferred to new address 0x8960…8525, no further transfers.
Hacker#6 Attacker Imitator-2, profit amount: 2,348,967.9 USDT
0x6e60…c5ea(BSC)
USDT exchanged across chains or multiple times for other tokens using tools like PancakeSwap, AnySwap (Multichain). Ultimately deposited 5,565.8 BNB to Tornado Cash; 630.4 ETH deposited to Tornado Cash.
Hacker#7 Arbitrage Bot-4, profit amount: 5,974.52 UNI, 1,667.36 MANA
0x6C6B…364e(ETH)
Exchanged for 30.17 ETH via Uniswap, of which 0.71 was paid to Flashbots, and the remaining ETH has not been further transferred.
Slow Mist's MistTrack will continue to follow up on this incident, monitoring the relevant addresses and conducting further hacker profiling analysis.