Essential Guide to Avoid Pitfalls in On-Chain Operations
This article is an original piece by Chain Catcher, authored by Gu Yu.
Blockchain technology is one of the most important innovations of our time, making decentralization truly possible. Anyone has absolute control over their on-chain assets, and external interference and manipulation are not possible.
This right comes with responsibility, meaning that users need to take 100% responsibility for the security of their assets. They must pay extra attention to private key storage and daily operations. Once a private key or mnemonic phrase is stolen, all assets face the risk of being stolen. Although many project teams (such as Tether) can theoretically control on-chain assets through smart contracts and recover stolen assets, they usually only provide assistance when a hacker deliberately attacks and causes significant losses. It is difficult to obtain assistance from project teams for asset losses caused by personal mistakes.
It is foreseeable that more and more trading activities will shift to on-chain, but unfortunately, on-chain scams are still emerging in large numbers and giving rise to many new forms. Several readers have reported to Chain Catcher that they have encountered on-chain scams and lost tens of thousands of yuan, with no way to recover the losses. To help more newcomers in the crypto industry understand some industry knowledge and avoid pitfalls, Chain Catcher has summarized some common scam tactics in this article, as follows:
1. Fake Coin Scams
Case: Xiao Ming is following a project that is conducting an IDO. In a Telegram group, he sees someone posting the token's smart contract address. After entering the address in Uniswap, he finds that trading is already possible, and there is liquidity worth hundreds of thousands of yuan. He immediately purchases 1 ETH, but when the price rises more than double and he prepares to sell, he discovers that the system prompts him that he cannot sell, effectively rendering it worthless.
Analysis: This situation falls under the fake coin scam. Some scam groups issue coins in bulk using names of popular coins, establish Uniswap trading pools, and inject a certain amount of liquidity to mislead users into thinking they are real coins, then spread the smart contract address through various social media channels.
However, the smart contract code of these tokens actually stipulates that only the issuer is allowed to sell the tokens, while other users can only buy but not sell. If users see the address on social media and believe it to be true, after buying the token, they can only watch its price rise and eventually go to zero.
According to observations by Chain Catcher, most fake coins on Uniswap are issued by a specific scam group, and each token issuer's address can be linked through transaction records. In the past two months, at least 70 fake coins have been issued, with profits exceeding 4,000 ETH.
In terms of specific tactics, they also transfer some fake coins to addresses marked as Binance, Vitalik Buterin, and 0x-b1 to attract the attention of followers of these addresses; each issuance activity lasts about 3-5 days, first adding hundreds of ETH in liquidity on Uniswap, then withdrawing all liquidity after very few purchases, and finally transferring all ETH to a new address to reissue new coins, occasionally transferring funds through Tornado.cash.
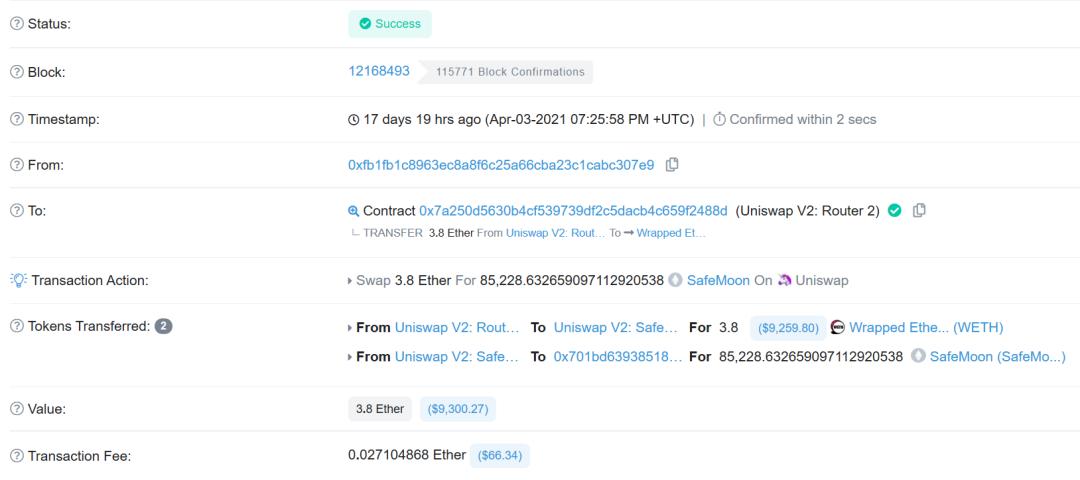
More misleadingly, these scam groups also create the illusion that certain whales are buying these coins. As shown in the image below, this address is widely believed to belong to Sun Yuchen, with assets worth billions of dollars. Over the course of ten days, Etherscan shows that this address purchased several new coins from Uniswap.
Some whale address trackers may see these records and "follow suit," but if they click on the specific transaction records, they can see that the trading behavior was not initiated by the owner of that address, but rather the fake coin issuer's address directly purchased from Uniswap using the smart contract and set Sun Yuchen's address as the receiving address.
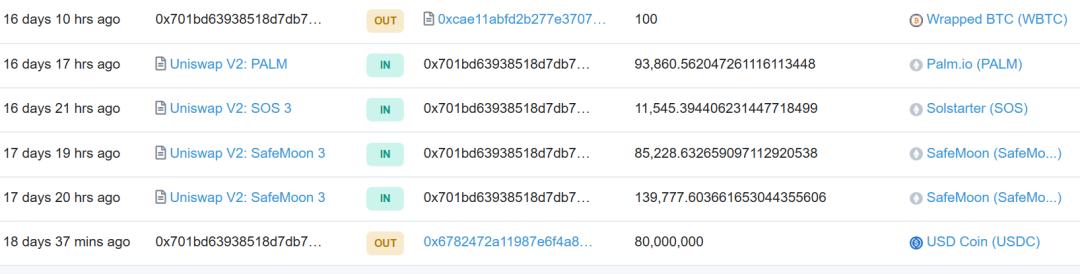
In addition to Sun Yuchen's address, many ETH whale addresses displayed on Etherscan have similar situations.
Therefore, when trading on Uniswap, it is crucial to use the contract addresses published by the official sources or the tokens listed in Uniswap's recommended list. Be cautious of smart contract addresses seen on other channels, as they may lead to significant losses.
2. Fake APP Scams
Case 1: Xiao Ni got a new phone and saw a user in a WeChat group claiming to be an imToken staff member posting a news image with an APP download link. Since he hadn't downloaded imToken on his new phone, he scanned the code to download the APP, entered his private key, and imported his wallet. However, he soon discovered that all assets in his address had been transferred out, resulting in a loss of nearly 20,000 yuan.
Case 2: According to The Washington Post, earlier this month, two users searching for the name of the crypto hardware wallet Trezor in the Apple App Store found an APP that used a logo and colors extremely similar to the real Trezor. Although Trezor had not launched a mobile APP at that time, they mistakenly believed that Trezor had indeed released a mobile version, so they downloaded it and imported their private keys, ultimately losing 17.1 bitcoins and ETH worth $14,000.
Analysis: Private keys and mnemonic phrases mean absolute control over wallet assets, so many scams attempt to extract users' private keys. Impersonating official APPs is one of the most common tactics. These fake APPs may either forge official news to lure users into downloading or pay for search engines to rank fake websites higher, or launch similarly named fake APPs in the official Apple/Android app stores. They closely mimic official websites and image information, and once users download the APP and import their mnemonic phrases, their wallet assets will be transferred away immediately.
Therefore, when downloading wallet or exchange APPs, always remember to download from official channels and check whether the website domain and other information are correct.
3. Fake Customer Service Scams
Case: Xiao Zhan encountered a problem while using a certain DApp product, so he went to a Telegram group to ask official personnel. Subsequently, a user privately messaged him to inquire about the situation and told him he could privately message an official staff member to resolve the issue and sent Xiao Zhan the account name. Xiao Zhan then clicked on the account name to enter the private chat interface.
The official personnel warmly asked Xiao Zhan what the issue was, stating that it was due to a database problem with the project and was being resolved. However, to avoid further errors, they needed to reset the account and asked Xiao Zhan what wallet he was using. They then provided a link and asked Xiao Zhan to input his mnemonic phrase to import the wallet for further operations. However, Xiao Zhan, being cautious, did not proceed with the next step, thus avoiding the leakage of his mnemonic phrase.
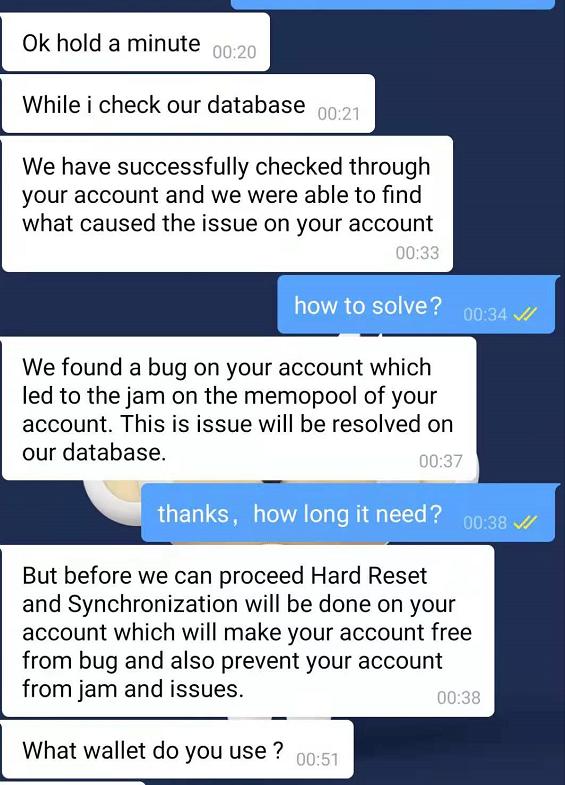
Analysis: Nowadays, almost all major social groups like WeChat and Telegram have accounts disguised as official customer service, using various methods to gain users' trust and steer the conversation towards wallets, enticing users to input their mnemonic phrases or private keys. Once users input them, all assets will be quickly transferred away.
Therefore, when seeking help in various communities, it is essential to confirm the identity of the other party. If unsure, you can take a screenshot and post it in the group to ask other active users for identification. Typically, official staff will not proactively message users to ask for their private keys but will instead encourage users to message them privately in the group chat.
4. Airdrop Scams
Case: Xiao Xi saw someone in a WeChat group posting information about an airdrop from a well-known project, stating that by completing a few specific social media tasks in a Telegram group, one could receive token rewards worth hundreds of dollars. Xiao Xi followed the prompts from the Telegram bot and completed all tasks, but later the bot prompted that he needed to send a small amount of tokens to the contract address to receive the airdrop tokens. Considering the cost was low, Xiao Xi sent the tokens as required but did not receive the airdrop tokens and instead lost over ten dollars.
Analysis: Token airdrops based on social media tasks do exist in large numbers, which can lower users' vigilance. However, it is precisely because of this that many scammers exploit users' lax mindset to implement scams, using airdrops to entice users to send tokens to smart contracts. Although the amount per transaction is usually not large, it can accumulate to a considerable sum.
Currently, there are no legitimate airdrop activities that require users to send tokens to external wallet addresses to receive them. Users should directly ignore any airdrop activities that require transferring tokens.
5. Points to Note
In addition to the aforementioned scams that need to be guarded against, on-chain operations still face many security risks caused by potential operational errors, mainly including the following points:
First, avoid excessive authorization to DApps and regularly clean up authorizations. Users need to authorize when interacting with a DApp for the first time, but this can pose risks. If the DApp is attacked afterward, it can directly use its permissions to steal user assets. Therefore, users should regularly clean up permissions for infrequently used DApps or set a limit on the amount of tokens that can be transferred.
Second, try to avoid using DApps that have not been audited by security companies, especially those claiming to have high APY, as their security risks may lead to significant losses of principal.
Third, it is important to emphasize again the need to securely store private keys and mnemonic phrases, preferably on hardware or notebooks that are not connected to the internet, and never disclose private keys and mnemonic phrases to any third party. This is the most important point among all security measures.
The vast imaginative space derived from blockchain technology and its larger-scale applications rely on more users having higher on-chain operational literacy and knowledge, so that on-chain does not become a lawless land filled with scams, causing many users to suffer significant losses unnecessarily. Therefore, the significance of the aforementioned popular science and education becomes particularly prominent.