Chainalysis Deep Dive Report: A Complete Guide to Cryptocurrency Services and Organization Categories
Source: Chainalysis
Compiled by: Chain Catcher
Since the launch of Bitcoin in 2009, cryptocurrencies have driven advancements in financial infrastructure and fostered innovative thinking on how to meet the demands of the global economy.
To promote the continued growth and adaptation of the cryptocurrency ecosystem, stakeholders such as governments, industry operators, and traditional financial institutions need to reach a common understanding of the participants in the cryptocurrency ecosystem. The key to identifying and safely seizing new opportunities is understanding which entities are conducting cryptocurrency transactions and the levels of risk and illicit activities associated with them.
In this guide, the cryptocurrency analysis firm Chainalysis provides an in-depth analysis of key participants in cryptocurrency transactions and their corresponding risk levels based on a comprehensive blockchain database and investigative experience. This includes entities involved in storing funds, investing and trading, purchasing/selling legal goods and services, purchasing/selling illegal goods and services, theft or fraud, etc. Each entity associated with these cases forms various cryptocurrency services and organizations.
1. Merchant Services
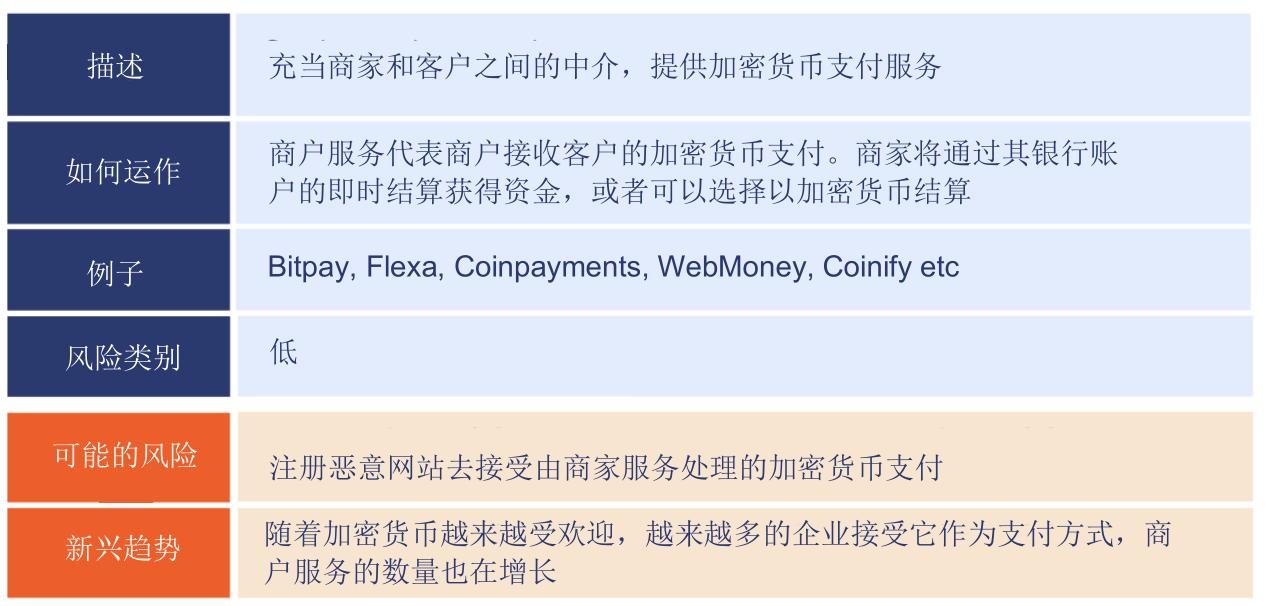
Merchant service providers allow mainstream businesses to accept cryptocurrencies as payment for customers' everyday purchases, whether online or in-person. They can be seen as conventional payment processors, like Stripe or Square, but compatible with cryptocurrencies. Merchant services enable people to use cryptocurrencies just like fiat currency.
Why would someone—consumers or businesses—want to use cryptocurrencies instead of fiat? There are many reasons, but the primary one is the reduction of fees. Traditional payment methods incur fees for each transaction, meaning businesses must either absorb the costs or pass them on to customers.
Cryptocurrency payments are more direct transactions, which means they are cheaper to process than credit card payments. This also applies to cross-border payments and remittances.
As cryptocurrencies become more popular, the adoption of merchant services is also increasing, with global companies like Starbucks and Whole Foods now accepting cryptocurrency payments. Overall, the use of merchant services has been on the rise since 2020, experiencing some dramatic spikes and drops during and after the Bitcoin price surge in 2017, following nearly two years of stagnation.
The commercial services category is generally considered a low-risk category. Users are typically traditional businesses and their customers. However, it is worth noting that scammers sometimes integrate merchant services with malicious websites to accept cryptocurrency payments from victims.
2. Custodial Wallets

To understand custodial wallets, it is essential to grasp how public and private keys support cryptocurrency transactions. Wallets manage and store users' public and private keys. In short, a public key is a digital, publicly-facing "identity" that represents where cryptocurrency can be received and sent from.
Your private key provides a mechanism to prove you own that public identity while keeping the private key confidential. It allows you to sign cryptocurrency transactions and send your funds elsewhere. If someone else knows your private key, they can effectively unlock all funds associated with it.
Non-custodial wallets (also known as self-custody wallets) allow users to store their public and private keys locally on their own devices, giving them full control over their funds at all times.
However, this comes with responsibility. Non-custodial wallet users are responsible for maintaining the security of their private keys to prevent hackers or any other parties from attempting to steal the keys and control the users' funds.
Custodial wallets (also known as hosted wallets) eliminate the inconvenience of users having to protect their keys by storing public and private keys within wallet infrastructure owned and maintained by the wallet service provider. This leads to a user experience similar to traditional banking and financial websites, making it easier for users to transact, albeit with less financial privacy and the risk of losing direct control over their funds.
Users should be wary of some malicious websites that mimic popular custodial wallet services to trick users into giving up their private keys and relinquishing control over their cryptocurrencies.
3. Mining Pools

The most commonly used mining process is known as Proof of Work (PoW) mining. In a PoW system, miners compete in a computational power guessing game. The first miner to find a valid answer gains the right to create a new block and add new transactions to the blockchain. As a reward for consuming all that computational energy, the miner receives newly generated cryptocurrency.
How difficult are the mathematical problems that power the blockchain to solve? Their difficulty is quantified by a metric called hash rate, which measures the total computational power expended to mine any given cryptocurrency; more computational power means more competition for each new block, making it harder for any single entity to win. Bitcoin's hash rate has grown exponentially since 2017.
In Bitcoin's early days, it was feasible for individuals to successfully mine new bitcoins using personal computers. However, with increased competition, this has become nearly impossible.
Miners respond by forming mining pools, where a group of miners combines their collective computational power to increase their chances of success. Competition is fierce, and some mining pools have entire server farms dedicated to mining. BTC.com and NiceHash are currently the two largest and most successful mining pools in operation.
Mining pools are considered a low-risk category because they receive the vast majority of cryptocurrencies through mining and distribute them to the individuals and groups participating in the mining pool. However, some mining pools accept donations or receive cryptocurrencies outside of mining, in which case they may be used for money laundering.
4. Exchanges

Exchanges allow users to buy, sell, and trade cryptocurrencies. They represent the most important and widely used service category in the cryptocurrency industry, accounting for 90% of all funds sent in the crypto services sector.
Since April 2020, exchanges have received over $1 trillion in cryptocurrency value, accounting for over 80% of all cryptocurrencies received by the crypto services industry.
Like wallets, exchanges can be custodial or non-custodial.
Custodial exchanges technically control your cryptocurrency because they hold the private keys associated with the wallets. Large, centralized retail exchanges tend to be custodial, as their brand names make them trustworthy for many users who are typically interested in fast transactions without needing to input private keys.
In fact, most transactions on exchanges are conducted off-chain, meaning they are not recorded on the blockchain but managed by the exchange itself, which is faster for users but reduces transparency. On-chain records of foreign exchange transactions only appear when users deposit or withdraw funds to or from addresses outside the exchange.
Exchanges may also handle fiat currencies differently. Cryptocurrency-to-fiat (C2F) exchanges, like Coinbase, allow users to exchange fiat currency for cryptocurrency, making them the primary platforms for entering and exiting crypto assets. This also means that C2F exchanges are the most common places for new users to acquire their first cryptocurrency.
On the other hand, cryptocurrency-to-cryptocurrency (C2C) exchanges only allow the exchange between different types of cryptocurrencies and are more favored by experienced users and high-frequency traders, who trade a wider variety of assets, not just the most popular coins.
Unlike custodial exchanges, non-custodial exchanges do not hold users' funds or the private keys associated with users' wallets. P2P trading is the most common example. Retail exchanges manage all transactions in a centralized order book, while P2P exchanges facilitate direct trades between individuals.
Users create a public listing showing how much cryptocurrency they want to buy or sell, and other users can respond directly and negotiate terms with them. Once terms are agreed upon, both parties can coordinate the transfer, whether in person or via direct wallet transfer, bank transfer, wire transfer, or gift card. P2P trading is particularly popular in regions without strong traditional banking structures, such as parts of Latin America and Africa.
While the most well-known exchanges strictly enforce "Know Your Customer" (KYC) protocols and use various tools to monitor transaction risks or illicit activities, other exchanges are much more lenient in compliance, exposing them to greater money laundering risks.
Overall, over $4 billion worth of cryptocurrency has been laundered through exchanges, including 300,000 bitcoins stolen in the Mt. Gox hack. However, as data shows, today's large exchanges place much greater emphasis on "anti-money laundering" compliance, significantly reducing the risk of allowing funds to be laundered.
5. Nested Services
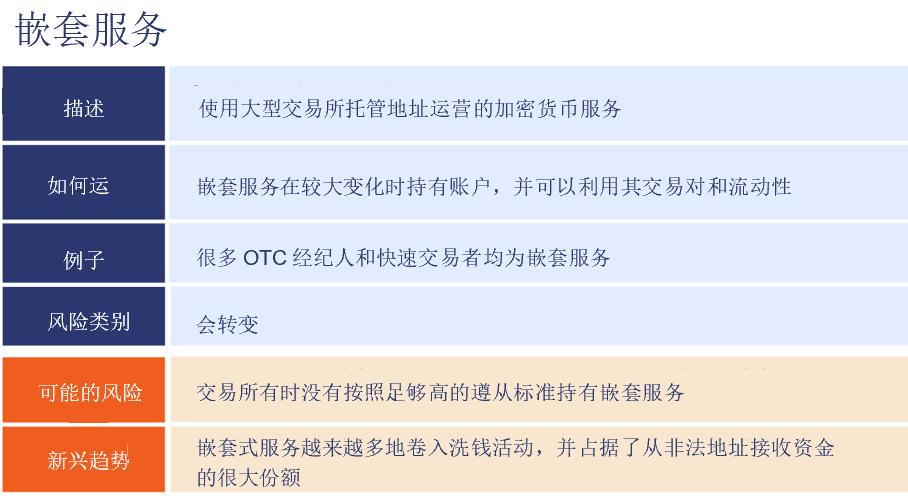
Nested services refer to cryptocurrency businesses that operate within one or more larger exchanges, leveraging the liquidity and trading combinations of those exchanges. Common examples of nested services include instant exchanges and over-the-counter (OTC) brokers, although both services can also operate independently.
While most nested services operate legally and compliantly, they disproportionately account for money laundering activities.
As noted in our 2021 Crypto Crime Report, a very small number of service-hosted deposit addresses account for the majority of cryptocurrency laundering, with just 270 addresses receiving 55% of all funds sent from illegal addresses in 2020. Most addresses receiving illicit funds are associated with nested services.
6. OTC Brokers

Over-the-counter (OTC) brokers facilitate large trades between individual buyers and sellers who cannot or do not want to trade on public exchanges. Many OTC brokers operate as nested services within one or more exchanges, but the largest ones often operate independently.
If traders wish to liquidate large amounts of cryptocurrency at an agreed price, they can work with OTC brokers. OTC brokers are a significant source of liquidity in the cryptocurrency market.
While we cannot measure the exact size of the OTC trading market, we know it is quite large. Cryptocurrency data provider Kaiko even estimates that online trading platforms account for the majority of all cryptocurrency trading volume.
While most OTC brokers operate legitimate businesses, some collaborate with criminal entities. Brokers on OTC trading platforms are often required to have KYC requirements lower than those of the exchanges they operate under.
Some take advantage of this to provide laundering services for criminals, helping them liquidate funds associated with illegal activities. Unethical OTC brokers often directly exchange illegally obtained cryptocurrencies for cash or use USDT as a stable intermediary currency.
On our website, we have seen examples of OTC acting as launderers, such as a massive Ponzi scheme that obtained billions of dollars worth of cryptocurrency from millions of investors. As of December 2019, PlusToken scammers transferred approximately $185 million worth of stolen bitcoins for liquidation. Most cash-outs resemble the trading patterns shown below, where hackers transferred large amounts of stolen funds through a series of intermediary wallets before transferring most of the funds to OTC brokers.
Additionally, many compliant exchange accounts have received substantial funds from illegal sources, with these accounts controlled by OTC brokers, many of whom have played roles in multiple criminal investigations we have participated in. However, most compliant OTC brokers remain a part of the cryptocurrency ecosystem.
7. DeFi
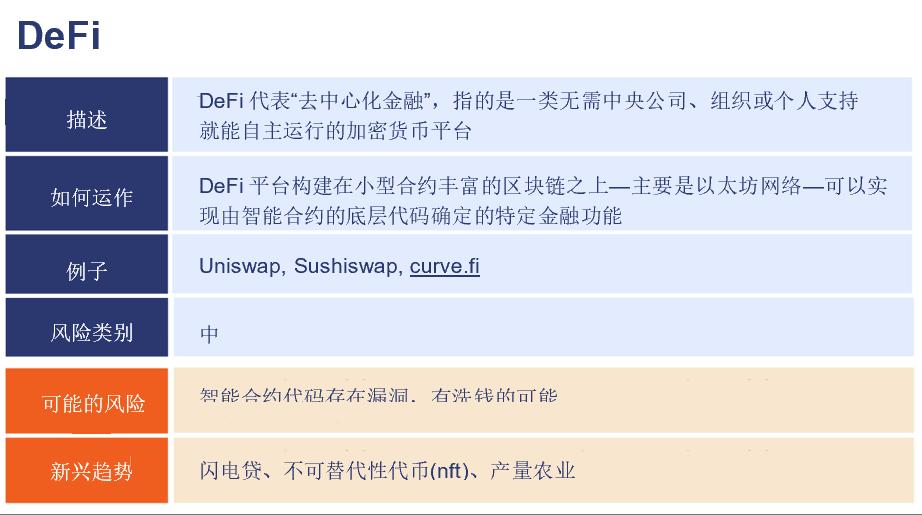
The growth of DeFi was one of the biggest stories in the cryptocurrency industry in 2020.
DeFi platforms are built on blockchain networks rich in smart contracts, such as Ethereum, and can execute specific financial functions determined by the underlying code of the smart contracts, automatically executing transactions and loans when certain conditions are met. DeFi platforms do not require centralized infrastructure or human governance, allowing users to execute financial transactions at lower costs than other fintech applications or financial institutions.
Overall, DeFi platforms received $86.5 billion worth of cryptocurrency in 2020, a 67-fold increase from the total in 2019.
Take decentralized exchanges as an example; these projects allow users to directly buy, sell, and trade different tokens built on specific blockchains between each other's wallets, enhancing privacy and security. Since these platforms never actually hold funds but facilitate direct transfers, users can complete these token swaps without providing KYC information or having their transactions recorded in an order book.
8. Cryptocurrency ATMs

Cryptocurrency ATMs are physical machines that allow users to convert cash into cryptocurrency and vice versa. As a quick and simple way to convert between cash and cryptocurrency, the primary concern regarding cryptocurrency ATMs is that they may attract criminals for money laundering. However, many cryptocurrency ATMs have robust KYC protocols, and the more cash users attempt to deposit, the stricter the requirements typically become. Users need to create accounts with personal identification information, such as a phone number or ID photo, making the risk relatively low.
The case against Kevin C. Fusco provides a good example of what cryptocurrency ATM KYC looks like in practice. It began with Fusco, a drug dealer active on multiple dark web markets, visiting a cryptocurrency ATM to exchange $32,000 worth of bitcoin for cash. The ATM flagged this transaction as risky, and when Fusco returned to attempt to exchange $200,000 worth of bitcoin, the ATM denied his request.
Because the ATM provider collected Fusco's driver's license information during registration as part of the KYC process, law enforcement was able to link these transactions to Fusco and use the ATM records to support their case when they ultimately arrested him.
9. Gambling
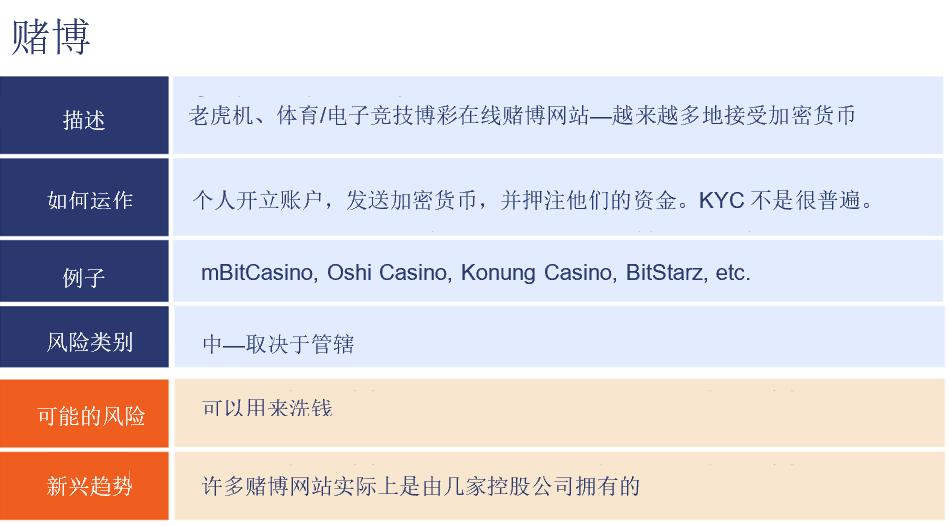
The online gambling world is an early adopter of cryptocurrencies, possibly because it allows users to gamble in jurisdictions where it is not permitted.
The risk profile of gambling services largely depends on jurisdiction. In the U.S., gambling websites are considered risky because most states do not permit gambling. However, in Europe, online gambling is entirely legal, so these services are considered low risk.
However, some gambling websites have lax KYC standards, making them potential targets for "money laundering." As with other categories, it is essential to dig deep into the practices of individual services when assessing risk.
Interestingly, many gambling websites rely on the same few payment processors to execute cryptocurrency transactions. While it may seem that customer payments across different addresses are deposited into each individual casino, the addresses are actually managed by a single third-party payment processor, which we refer to as nested services in this arrangement.
10. Network Infrastructure Services
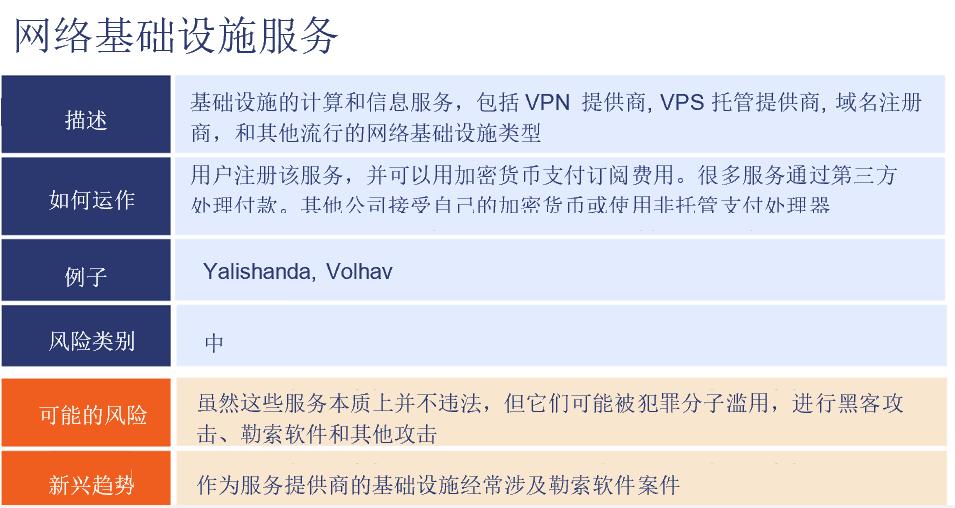
Network infrastructure refers to the services necessary to operate a website or other internet-based business. This includes virtual hosting, domain registration, email and other communication services, e-commerce postage services, etc.
Many network infrastructure providers accept cryptocurrency payments. While they typically do so through merchant service providers, we can often identify specific merchant service addresses used by particular multi-dimensional data center infrastructure providers.
We classify network infrastructure providers as medium-risk cryptocurrency services because they often offer anonymous features, making them popular among cybercriminals.
One example is the web hosting service BlackHost, which is known for its so-called bulletproof hosting services, meaning it allows customers to pay for services anonymously and is generally lenient about the types of content they allow to be hosted.
11. Mixers

Mixers are services that help users conduct transactions with greater privacy and obfuscate the source of funds. This capability, combined with the fact that most mixers have no KYC requirements, makes them a common mechanism for money laundering. In fact, we find that mixers are the most popular cash-out locations for illicit activity funds.
Mixers create a disconnect between the cryptocurrency funds deposited by users and the funds they withdraw, making it more challenging to trace the flow of funds. They pool all user deposits together and then mix them randomly. Users can then withdraw their deposited funds from such platforms, minus a service fee of 1-3%.
Some mixers allow users to receive different amounts of funds at staggered times and different addresses, making the funds harder to track. Others attempt to obscure the fact that mixers are being used by changing the fees for each transaction or altering the types of deposit addresses used.
While mixers are not entirely illegal, law enforcement has been increasingly scrutinizing them and shutting down those that have received large amounts of illicit funds.
Mixers have more legitimate use cases for private transactions. However, given their built-in features that facilitate money laundering and the previous shutdowns of large, established mixers, financial institutions and cryptocurrency businesses may scrutinize their exposure to mixers more thoroughly than other services.
12. Dark Web
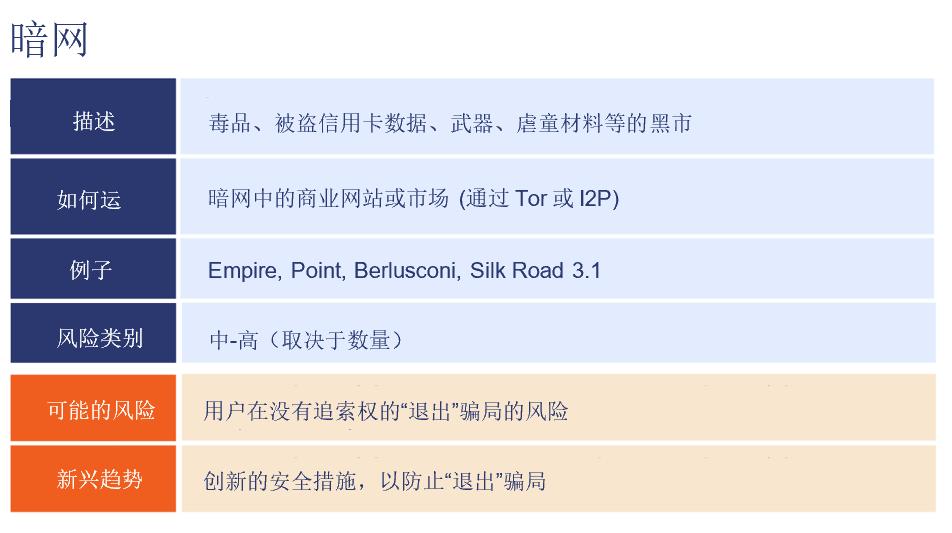
Dark web markets are commercial websites similar to eBay, where users can buy and sell goods using cryptocurrencies. Of course, their primary distinction is that most goods are illegal, including drugs, tools, weapons, stolen credit card data, child sexual abuse materials, and more.
Dark markets are typically only accessible through anonymous services like Tor and I2P. Dark web markets are among our highest-risk categories, and any addresses or services with significant exposure to dark web markets may come under scrutiny from regulators.
In 2020, we saw an increasing number of dark web markets adopting new, decentralized business models, making them harder to shut down. One example is Televend, a platform based on Telegram with over 150,000 users. On this platform, dark web sellers can sell drugs through automated chatbots (which communicate with buyers in highly encrypted ways), and buyers can find a directory of drug suppliers categorized by region and product type by simply visiting Televend's Telegram group. There, they can place orders with the selected supplier's chatbot, receive an automatically generated bitcoin address, then make payment and wait for the drugs to arrive by mail.
Televend takes a commission from each transaction but never actually touches the funds, making it easier for law enforcement to blend in with transactions that are harder to track through blockchain analysis.
We expect that in 2021, platforms like Televend will continue to grow and capture a larger share of the total market revenue on the dark web, as their decentralized nature makes them more resilient to attacks from law enforcement and competing markets.
13. Stolen Funds

Theft is one of the biggest problems in cryptocurrency, with over $500 million worth stolen in 2020, and total theft amounts reaching billions of dollars. Almost all cryptocurrency theft cases can be categorized into three types: exchange address attacks, individual address attacks, and DeFi attacks.
Hackers have stolen billions of dollars worth of cryptocurrency by attacking the wallets of exchanges. Bitpoint, Binance, DragonEx, and several other companies have been targets.
More common than exchange attacks are attacks on individual cryptocurrency holders, which are primarily conducted through phishing or social engineering. However, we know that due to underreporting, these numbers are almost certainly lower than the true total—many people do not report stolen cryptocurrencies to authorities.
With the increase in DeFi usage in 2020, the amount stolen from DeFi platforms has also risen. Data indicates that DeFi platforms are particularly vulnerable to attacks, with 33% of all cryptocurrency stolen in 2020 coming from DeFi platforms, despite accounting for only 6% of all cryptocurrency activity.
14. Illicit Actors/Organizations
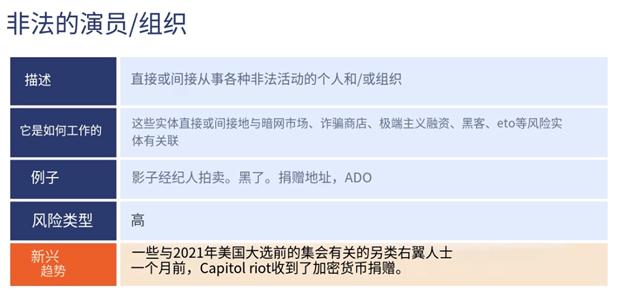
Illicit actor organizations refer to groups that engage in transactions with cryptocurrencies whose activities may not necessarily rise to the level of criminality but are still considered risky due to proximity to illegal activities or reputational risks.
One example is websites implicitly associated with sex work, such as RubRatings, which allows female massage therapists to post advertisements soliciting clients and accepts bitcoin as a payment option. While massage is clearly legal, the language on RubRatings suggests that sexual services can be obtained, and the service is listed as a facilitator of human trafficking, so we classify it as an illicit actor organization.
Another example includes organizations and public figures associated with domestic extremism and racial hatred. Many of these organizations accept cryptocurrency donations, and we expect that as they continue to withdraw from traditional payment platforms and social media networks, more organizations will accept cryptocurrency donations.
In most jurisdictions, extremist speech is not illegal in itself, but many extremist organizations are associated with violent events, such as the 2017 Unite the Right rally in Charlottesville, Virginia, or the 2021 U.S. Capitol riot.
In the latter case, several alt-right individuals, including some directly linked to the rally before the riot, received substantial bitcoin donations a month prior.
15. Ransomware
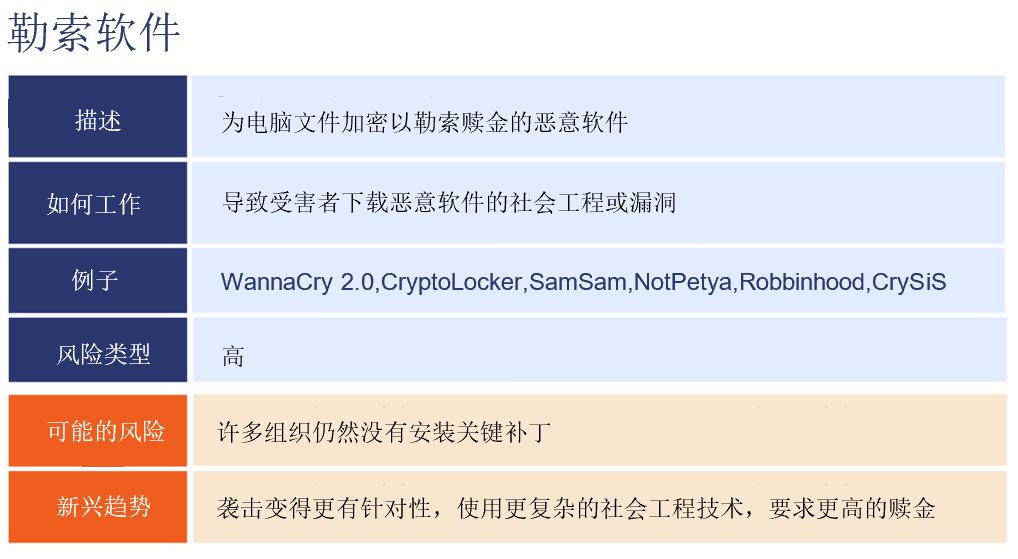
Ransomware is a form of cybercrime in which hackers inject malicious software into users' computers, encrypting all files within. The hackers then demand a ransom from users to regain access to these files, typically in cryptocurrency.
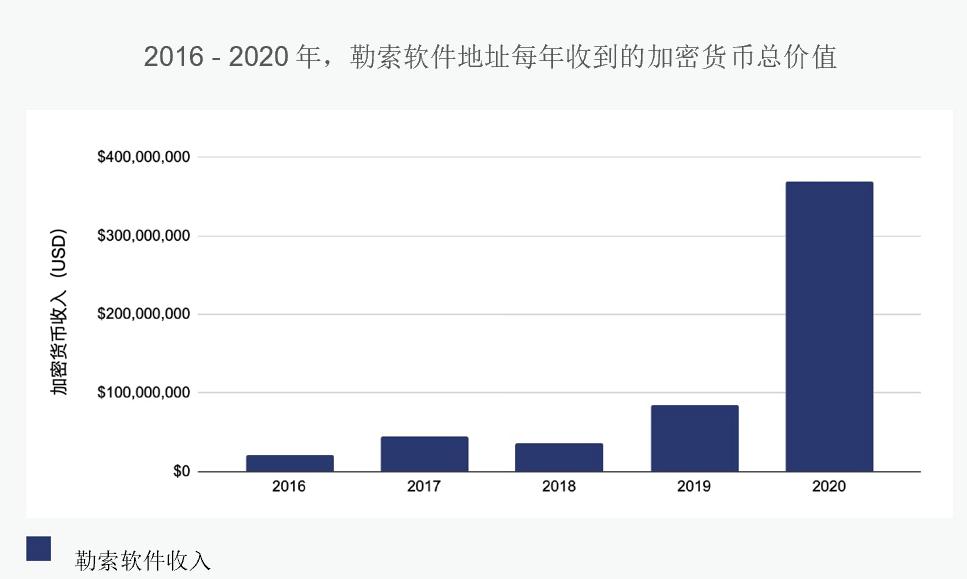
In 2020, ransomware attacks surged dramatically with the outbreak of the COVID-19 pandemic. Blockchain analysis shows that the total amount paid by ransomware victims increased by 336% that year, reaching nearly $370 million in cryptocurrency. The range of victim organizations has been very broad over the years, including schools, hospitals, and even local municipalities.
Cybersecurity experts recommend that if businesses are attacked by ransomware, they should immediately contact law enforcement and provide the payment address. Investigators can then use blockchain analysis software to examine the flow of funds in and out of that address, identify the services used to convert funds and cash by the ransomware operators, and hope to link the addresses to real-world entities.
16. Terrorism Financing
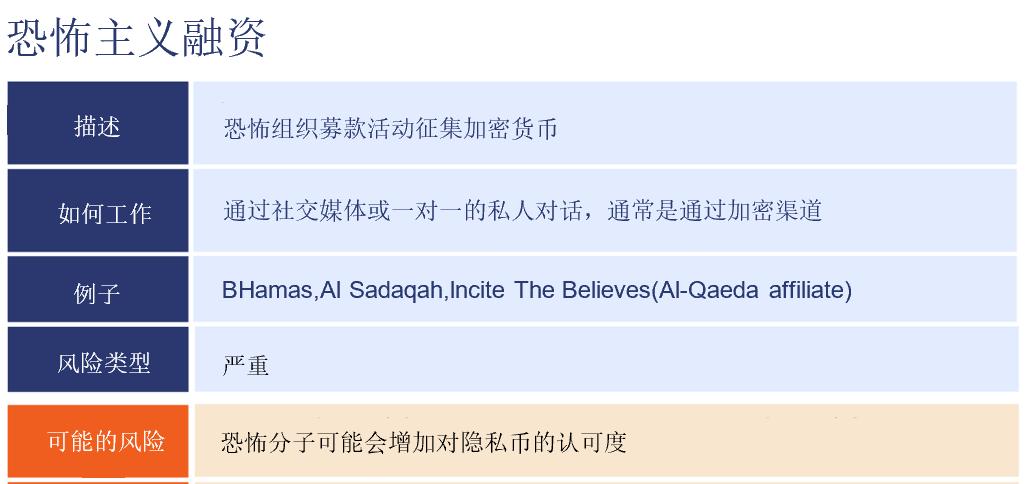
Terrorist organizations are increasingly using cryptocurrencies to raise funds, often through public fundraising campaigns and one-on-one conversations on private encrypted chat applications to solicit donations.
Terrorist organizations often make it very clear what these donations will be used for. Take a look at the poster created by the Gaza-based organization Jaysh Al-Ummah. They tell potential donors that their donations to the bitcoin address in the advertisement (which has been obscured) will help their fighters purchase weapons.

While the amount of cryptocurrency donated to terrorists is generally small at present, the ability of these organizations to receive donations relatively smoothly from anyone in the world represents a disturbing trend. Not to mention, the cost of carrying out terrorist attacks is very low.
As the Deputy Secretary of the Treasury for Terrorism and Financial Intelligence Sigal Mandelker stated, remittances associated with suspected terrorism average only $600, which is more than enough to purchase a homemade suicide bomb or similar weapon. With the continuous improvement of technologies that support anonymity, such as mixers, this activity may grow.
17. Sanctions
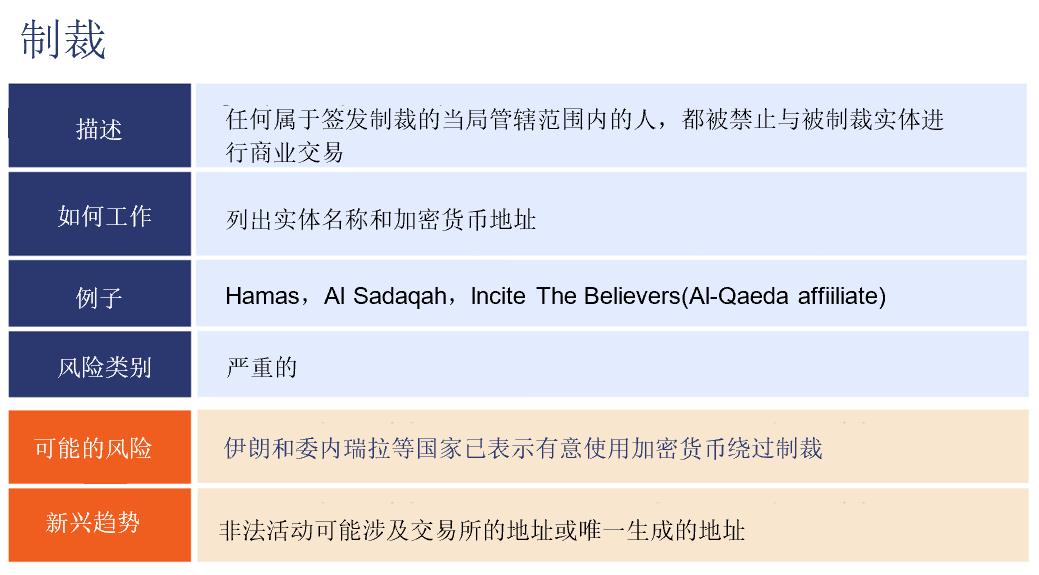
Sanctions are issued by governments to designate individuals and organizations that citizens are prohibited from doing business with. Sanctions typically encompass not only the sanctioned entities themselves but also any tools owned or controlled by those entities, including operating companies, bank accounts, and, more recently, cryptocurrency addresses.
In general, any exposure of a sanctioned cryptocurrency address may lead to heightened scrutiny of cryptocurrency businesses and financial institutions cooperating with those cryptocurrency businesses, including potential obligations to block asset transfers or return them to designated senders or otherwise benefit designated entities, such as debt forgiveness.
18. Child Sexual Abuse Material Websites
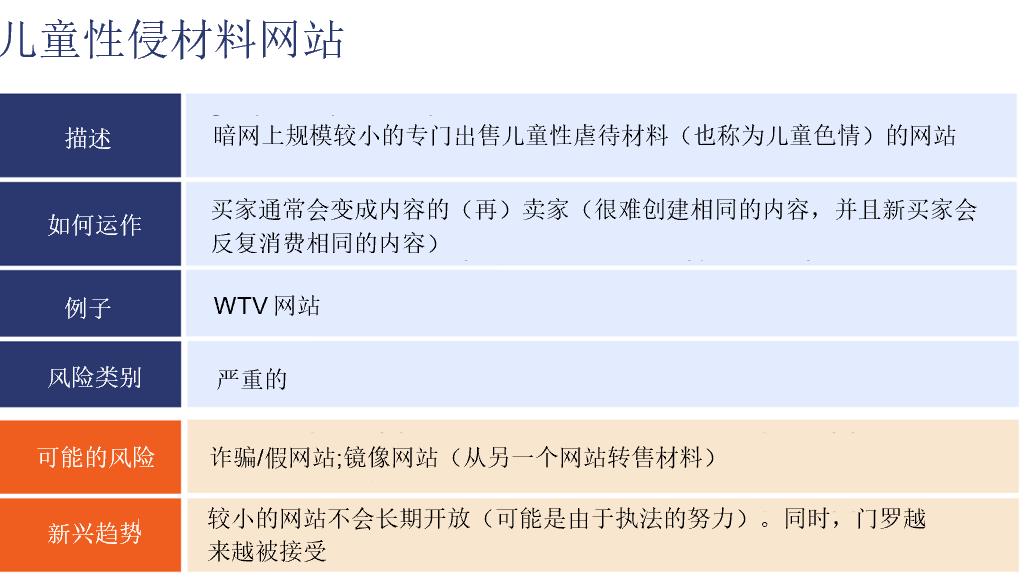
A small number of opaque dark web sites specialize in selling child sexual abuse material (CSAM), often facilitating transactions using cryptocurrencies. Most mainstream dark web markets prohibit such material, necessitating dedicated stores. Markets centered around CSAM typically do not operate for long, possibly due to law enforcement actions and efforts by those operating the sites to avoid detection.
Some CSAM websites function similarly to dark web markets, gathering buyers and sellers in a central marketplace. Others are exclusive sellers, and some require users to upload their own CSAM content to access the site's content. Typically, users will purchase CSAM on one site and then resell it elsewhere.
In 2018, Chainalysis collaborated with the IRS Criminal Investigation Division, the Department of Homeland Security, and other global law enforcement agencies to shut down WTV, the largest known CSAM website (by available material).
The public knows very little about how these sites operate, so WTV provides a useful case study. WTV operated outside of South Korea, allowing users to purchase CSAM with bitcoin or upload their own content in exchange for points, which could then be used to download more content.
Users received their own unique bitcoin address when registering to use the site, and they would send funds to that address in exchange for content. WTV had 1.3 million bitcoin addresses ready to be allocated at the time it was shut down, indicating it could support a massive user base. Between 2015 and 2018, the site received over $353,000 in payments.