A Comprehensive Analysis of the Power Machinery Behind Ethereum: MEV and PBS
Author: Masterdai
Source: Hash Hunter
In 2007, a trader at the Royal Bank of Canada named Shengshan discovered something puzzling: the moment he pressed the buy button on his trading terminal, all his orders disappeared.
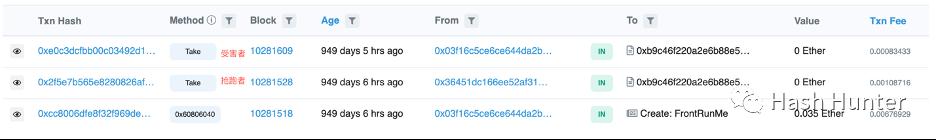
A similar incident occurred in the world of blockchain. In June 2022, Scott Bigelow deployed a crypto contract on the Ethereum mainnet and deposited 0.035 Ether into it, with only he knowing the password to withdraw the funds from the contract. However, the moment he sent the password to the contract, the Ether disappeared.
Undoubtedly, they both encountered a frontrunner. Shengshan's orders were spread across various exchanges, and due to geographical reasons, there were slight differences in the time it took for each order to reach its respective exchange. High-frequency traders, using faster fiber-optic networks, learned about the first buy order ahead of time and bought up all the orders before Shengshan's could be placed on other exchanges.
Although Scott's password was known only to him, it was sniffed out by frontrunners in the mempool before his transaction information was broadcast to various nodes, allowing them to copy his password and preemptively withdraw the funds from the contract by paying a higher gas fee. These frontrunning bots are just the tip of the iceberg of these "predator" activities. Unlike traditional finance's high-frequency trading, the dark forest of blockchain, which has no entry barriers, has seen the emergence of more sophisticated and ruthless strategies, widely applied in DeFi and NFT sectors.
This article will showcase the roles of MEV bots and Flashbots from the perspective of Ethereum's underlying principles; the impact of the PBS architecture on the subsequent crypto ecosystem and predictions for the evolution of various roles in the future. It is divided into three chapters:
The first chapter is an interpretation of the principles.
The second chapter elaborates on the ecological landscape of MEV, investment, and entrepreneurial opportunities.
The third chapter predicts and looks forward to the future of the proposer-builder separation architecture.
1. Industry Chain
To fully understand the current PBS ecosystem (proposer-builder separation), we can view it from the user's perspective when initiating a transaction: "What exactly happens from the moment a user interacts with a decentralized application until it is fully established on the consensus layer?"
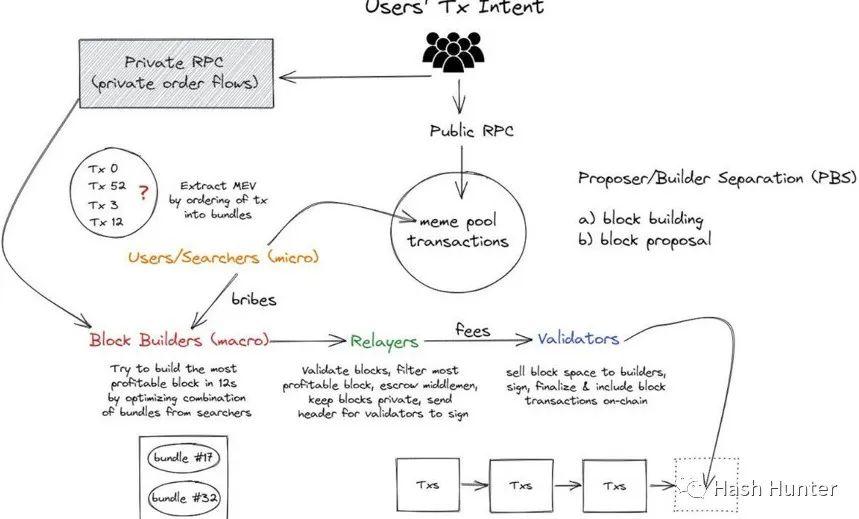
For ease of understanding, I have broken down these processes into several steps:
User Transaction: When we transfer funds in our wallet or exchange tokens on a decentralized exchange or mint an NFT, the on-chain data structure is similar.
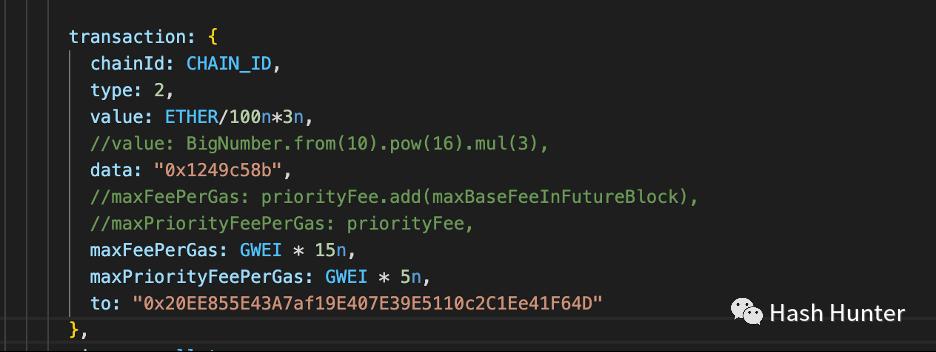
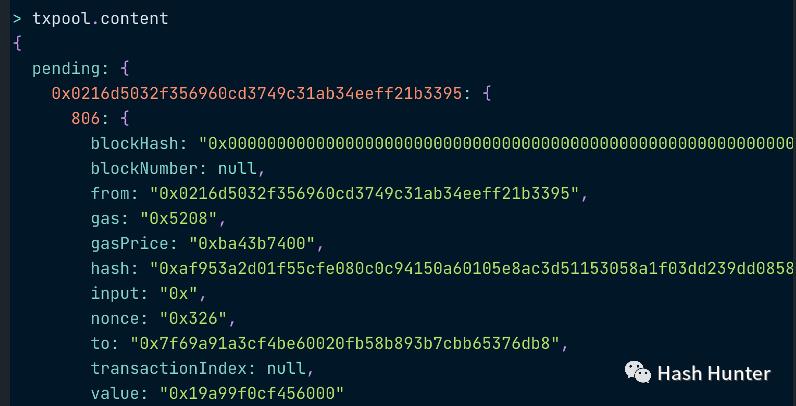
The above image shows the information required to mint an NFT contract, with the most important piece of information being the data. In the data, 0x1249c58b represents the call to the mint() function. If we replace the data with 0x, it signifies a regular transfer. Through this data and value, we can clearly determine the user's intent and purpose for the transaction.
Mempool: When users remotely call services using public nodes (e.g., Metamask defaults to using Infura's Ethereum node), the transaction enters the mempool. The mempool is a buffer where nodes receive transactions and include them in blocks, helping nodes check various transactions and determine the legality and validity of the outputs and signatures.
Transactions in the mempool are different for each node, but the data they contain is public across the entire blockchain network. In other words, anyone who can set up nodes on cloud servers worldwide can access most of the mempool data. The misuse of mempool data is extremely unfriendly to ordinary users. As illustrated in the opening case, arbitrageurs can anticipate users' transaction intentions and profit from them. This profit-making process is referred to as MEV (Maximal Extractable Value).
Searcher: Also known as Ethereum bot operators, the arbitrageurs and NFT mint bots we currently understand fall into this category. Searchers are closely related to Flashbots; after Flashbots open-sourced their auction components, searchers can send bundles of their transactions or mempool transactions in sequence and specify a particular block builder to include these transactions in the block, thus avoiding their transactions being sniffed in the public mempool.
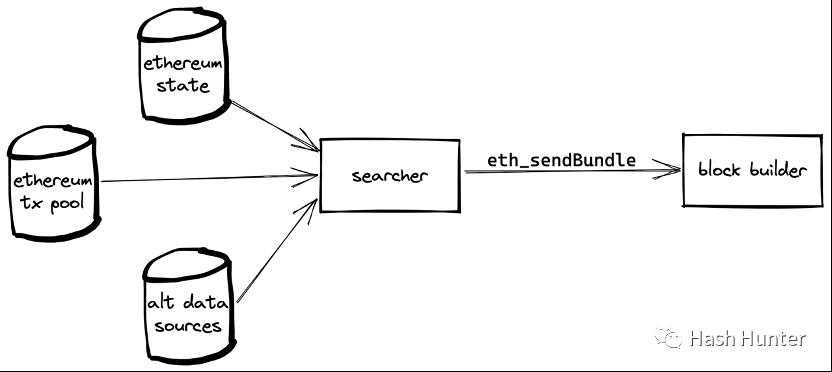
Flashbots have effectively created a new channel for transaction information, allowing some users to communicate directly with block builders. For example, in the following case, I used Flashbots to directly relay the mint transaction details to the block builder, thereby avoiding my mint information being known in advance.
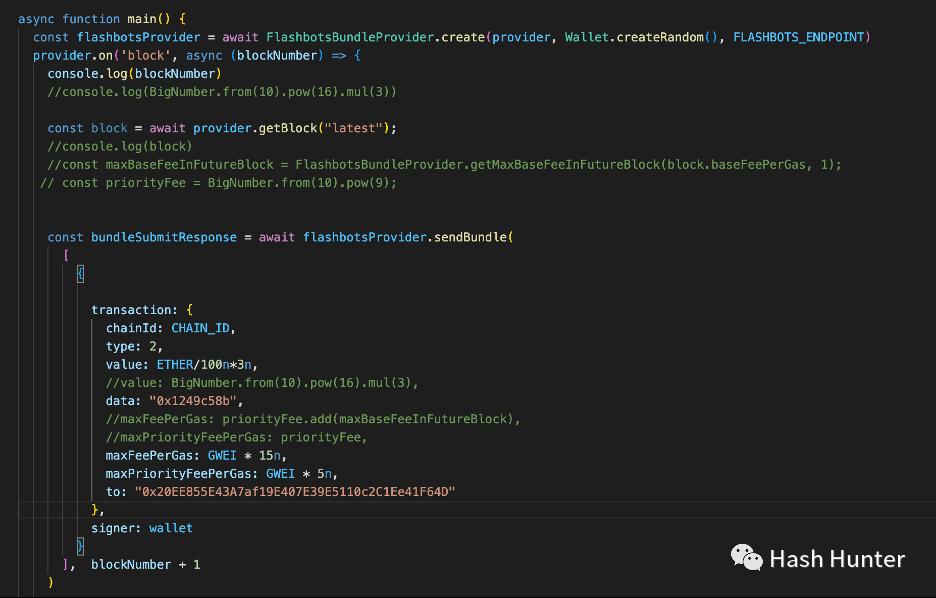
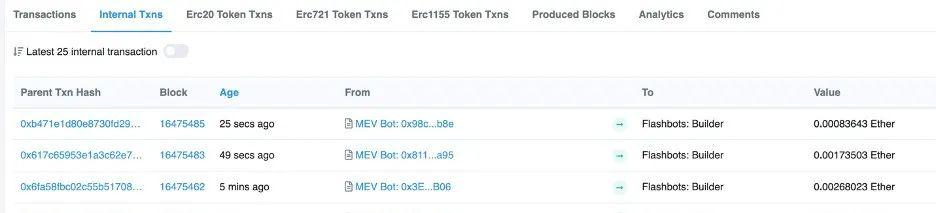
Searchers also need to pay a certain price to make their bundles more attractive, such as increasing gas fees or directly transferring Ether to the builder's Coinbase address.
Through the bundling mechanism, searchers have the ability to change the order of transactions within a small range. Mechanically, it can ensure that transactions arranged in order have a chance of not being interrupted. By combining external transactions and their own contract call transactions, various attack strategies in the MEV domain are formed, such as frontrunning, backrunning, sandwich attacks, JIT bots, time thief attacks, and uncle block thief attacks, etc.
a. Frontrunning: Profiting by preemptively and copying opponents' transaction strategies. For example, minting an NFT ahead of ordinary users by paying a higher gas fee, seizing the mint share from human users, etc.
b. Backrunning: Profiting by competing for the subsequent position of a transaction. Bots monitor certain tokens creating new trading pairs on Uniswap and create a large number of buy transactions after the pool is deployed. This strategy aims to be the first to purchase the token. Similarly, bots can monitor NFT projects activating the mint() transaction to become the first to mint the NFT. Most existing NFT minting bots on the market are designed based on this principle and architecture.
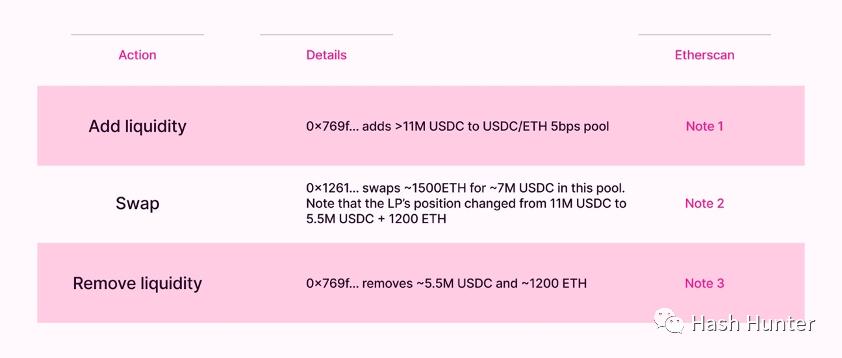
c. Sandwich Attack: When a user wants to swap for token A on a decentralized exchange, the bot can create two transactions and use the bundling feature to sandwich the victim's transaction. The bot's first transaction buys token A, the victim's transaction then pushes up the price of token A, and the third transaction sells the same amount of token A to profit. The profit depends on the slippage set by the victim's transaction.
d. JIT Bots (Just In Time): This mode appears in Uniswap V3's token pools. Due to V3's concentrated liquidity feature, users can set an LP within a very narrow range. When a user wants to conduct a large token transaction on V3, they immediately initiate a liquidity addition transaction and a liquidity destruction transaction, sandwiching the user's transaction to capture the liquidity income generated by this transaction. This mode requires JIT bots to calculate the position changes of the front and back transactions in advance, ensuring that the user's transaction falls exactly within the designed liquidity range.
Due to space limitations, I will not detail the specific attack methods and steps in this article. Interested readers can visit here (https://www.mev.wiki/attack-examples). Not all searchers are arbitrageurs. We can also use these mechanisms for good.
a. Transfer Service: Some hackers exploit NFTs in stolen wallets to conduct phishing. Usually, the ETH in these wallets is insufficient to cover the gas fees for transfers. When victims attempt to transfer gas to make the transfer, hackers use scripts to steal the gas fees. We can use Flashbots to retrieve the NFTs from the stolen wallet before the hacker takes the gas fees you transferred.
Set up a transaction to transfer into the stolen wallet, then create a transaction to transfer out from the victim's wallet, placing these two transactions in a bundle and sending them to the block builder. Since these two transactions are consecutive in the block, hackers cannot prevent you from transferring out the stolen NFT. When a searcher completes the bundle construction, they can send this bundle to their designated block builder.
Block Builder: Thanks to Flashbots open-sourcing the block building architecture in November 2022, we can understand the internal design of block builders. A complete block building client consists of two different nodes: a Geth execution layer node program with block building specifications and a modified Prysm consensus layer node.
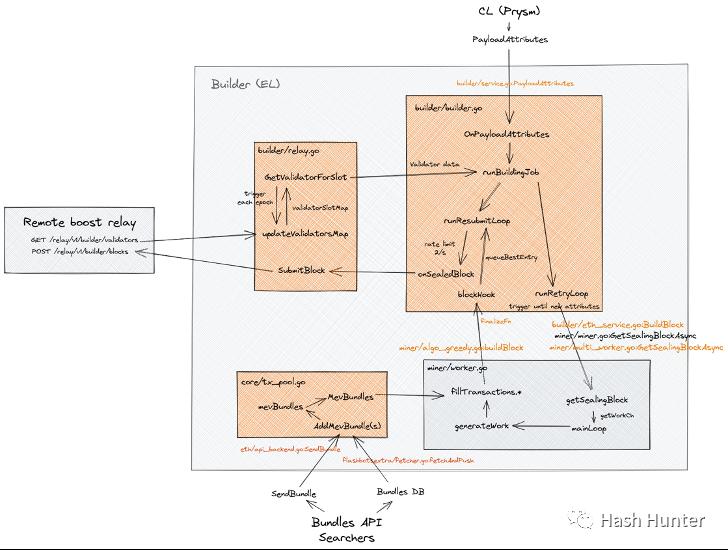
Block builders need to open an RPC endpoint so that searchers can send bundles to designated builders. The builder itself is divided into two modules: miner (Geth) and builder (Prysm). The miner module selects bundles that meet its program requirements and picks transactions from the mempool to include in the created block through an algorithm.
The builder module continuously communicates with the relayer and miner modules while generating block data, including the block's hash, recipient address, and additional information (usually the builder's name is included). It also sets up a transaction to send the entire block's revenue to the recipient address of the validating nodes.

Relayer: Block builders need a trusted third party to deliver the blocks they send to validators without leaking them. Similarly, validators also need a trusted relayer layer to ensure the legality of the blocks. Of course, different relayers have their own characteristics. A validator can connect to multiple relayers through MEV-Boost to gain the maximum block selection rights.
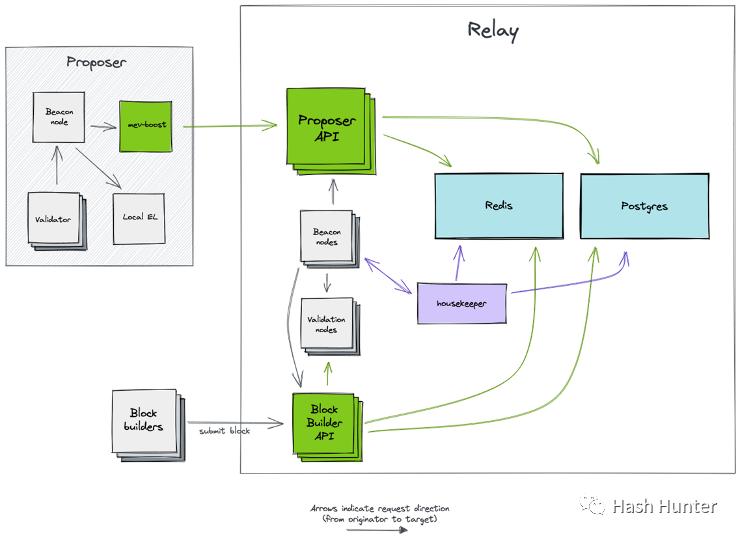
From the above architecture, we can see that relayers also need to run consensus layer nodes and execution layer nodes to receive and send block information. The relayer has two external APIs connecting to block builders and MEV-Boost. This architecture maximizes the reduction of communication and trust costs between proposers and builders while ensuring that block information is not leaked.
Proposer: After the Ethereum merge, a new consensus layer was added to the network. The proposer architecture consists of four clients: execution layer node, consensus layer node, validator (32 ETH), and MEV-Boost. This is also the underlying architecture for most Ethereum node stakers. The original node stakers consisted of the first three software, and MEV-Boost can be understood as a plugin to coordinate communication between the two nodes and obtain additional block information from the relayer layer.
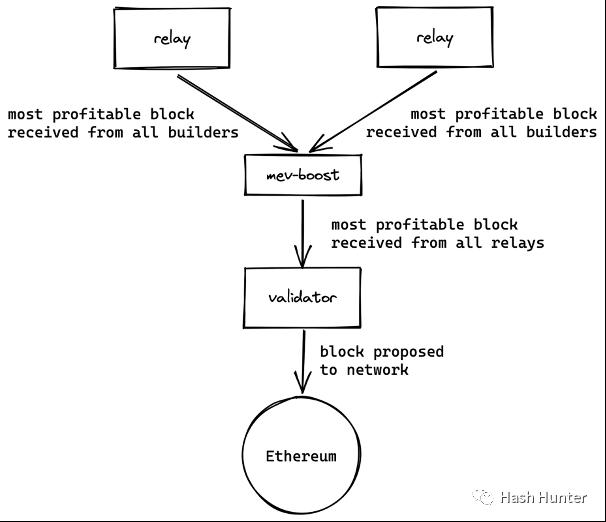
This architecture effectively separates the original proposer's ability to build blocks, allowing proposers to simply propose blocks from MEV-Boost and add them to the beacon chain. Similarly, MEV-Boost can connect to multiple relayer layers, maximizing the proposer's interests. Ultimately, the profits generated by searchers and blocks are paid to the proposer, i.e., Ethereum stakers.
Transaction Chain:
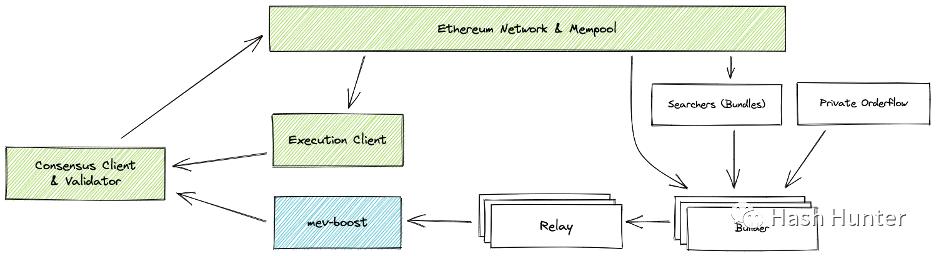
When a user initiates a transaction, it first enters the public mempool. If this is a regular transaction, it will be included in the block created by the block builder after waiting for a while. If it is a transaction targeted by a searcher, it will enter the block in the form of a bundle. It then goes through the relayer and is ultimately signed and broadcast to the network by the block proposer. Users can also use private nodes from block builders to bypass the public mempool.
Revenue Chain: Searchers look for transactions in the mempool that can capture profits, retrieve these transactions, and combine them with their own created transactions to place them in a bundle. The profits obtained by searchers go directly into their wallets, and to have this transaction included in the block by the block builder, searchers need to pay a fee to the block builder (through gas or Coinbase transfer).
a. Block Builder's Revenue = Transaction Fees (Gas) + Searcher Paid Fees - Burned Gas Fees
b. Block Builder's Profit = Transaction Fees (Gas) + Searcher Paid Fees - Burned Gas Fees - Block Builder's Fees to Validators (Costs)
c. MEV-Boost Revenue = Last Transfer in the Block = Block Builder's Fees to Validators (Costs)
Taking block 16489407 as an example, the overall block reward displayed on Etherscan is 0.129830707718222266 Ether, which is not the actual profit from block building, but merely the transaction fees - burned gas fees. Records of coinbase.transfer can be queried from Flashbots' address, showing that the searcher paid a total of 0.16601722521 Ether in fees.
Of course, this block actually contains 6 bundles, with the remaining 4 bundles being paid in the form of gas fees. Due to space limitations, I will not elaborate further here; I will write a detailed article in the future on how to calculate the MEV revenue of a block.
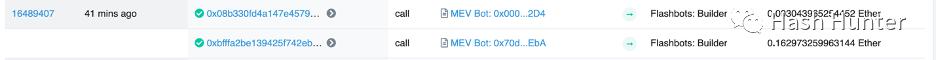
In the last transfer of this block, the builder transferred 0.295569746890668 Ether to the validator.

Calculating gives:
Block Builder's Revenue = 0.129830707718222266 + 0.16601722521 = 0.29584793292 Ether
Block Builder's Profit = 0.29584793292 - 0.295569746890668 = 0.00027818602 Ether
From this, we can see that the block builder's profit is not as high as we might imagine, and the majority of MEV profits still go to the validator nodes that have installed MEV-Boost. It is important to note that the revenue here does not include the staking rewards of the nodes. A node staker's revenue is divided into consensus layer revenue and MEV-Boost revenue.
MEV-Boost revenue is cash for validators; if a staker is lucky, they can receive ETH-settled revenue directly from the fee address after installing Boost. The consensus layer revenue has a billing period and can only be withdrawn after the Shanghai upgrade.
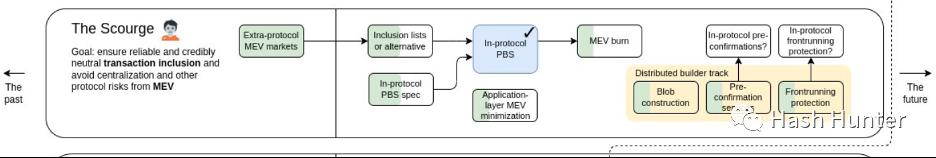
From the overall technical architecture and chain perspective, the current PBS architecture design is not simple. PBS itself is also a transition for Ethereum before the Scourge phase. The collusion between the relayer and builder layers and the centralization of block builders have not yet been completely resolved. This is also a major reason why Flashbots launched Suave later.
2. Ecological Landscape and Investment Opportunities
The previous chapter categorized and organized the MEV chain through the implementation of the underlying architecture. In the ecosystem, project parties often occupy multiple fields and directions to achieve profitability and creation. Of course, this field is still in a very early stage, and there are currently no clear business models or leading players in the race. To assess these early projects, I have roughly divided them into several tracks (not involving node stakers) and measured them from three aspects: whether they can generate profits, whether they have the conditions for large-scale commercialization, and whether they are sustainable.
Searchers: Based on their functions and sources of profit, they are divided into arbitrageurs, sandwich attackers, and liquidators. Their profit areas cover decentralized trading, lending, NFT trading, flash loans, etc. From the data provided by EigenPhi, we can see that the profit distribution among searchers is extremely unequal.
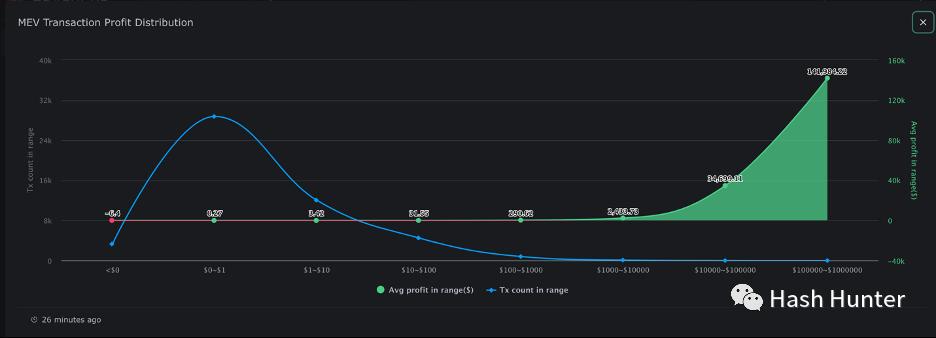
The vast majority of arbitrage profits are concentrated around $0.27, while only a very small number of arbitrage profits exceed $1,000. At the same time, searchers also face the risk of being trapped by peers and subjected to reverse arbitrage (salmonella tokens). Nathan Worsley stated in his MEV Day speech: "This field requires top talent for team collaboration; 20 small teams occupy the vast majority of the market share, and arbitrage strategies are becoming increasingly complex and competitive."
The intense competition among searchers largely stems from the openness and lack of entry barriers in blockchain networks. On one hand, they need better servers and faster information transmission channels to obtain the latest mempool data; on the other hand, they also need clever algorithms and strategies to ensure they can profit without being captured by others.
Undoubtedly, the searcher domain is a track capable of generating profits and having sustainability, but this field does not possess the potential for commercialization aimed at the general public; it resembles quantitative trading in the crypto space. For large investment institutions, investing in an on-chain quantitative trading team may not yield high returns. However, for small entrepreneurial teams and individuals familiar with quantitative trading and smart contract development, this may be a relatively good practice to enter the crypto field. For example, establishing a crypto quantitative fund and promising xx% returns. Of course, this field is not static. The recent surge in trading volume of JIT bots is a testament to that.
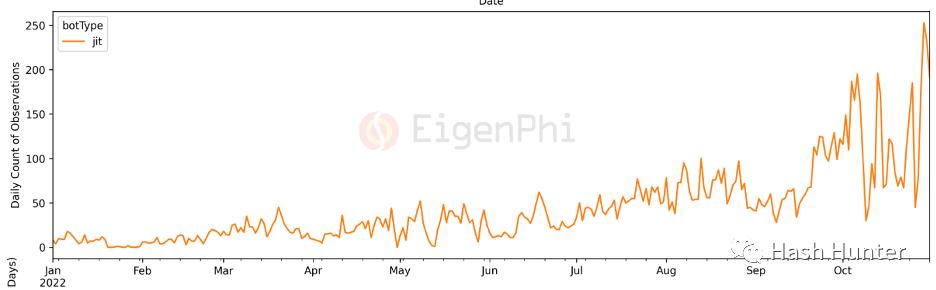
With the increase in on-chain trading users and the emergence of various new DeFi protocols, there will be a plethora of new profit opportunities in the future. This will test the execution capabilities of the teams themselves and their understanding of on-chain protocols.
Builders: According to current on-chain data, the builder market faces relatively intense competition, with more and more node service providers entering this market.
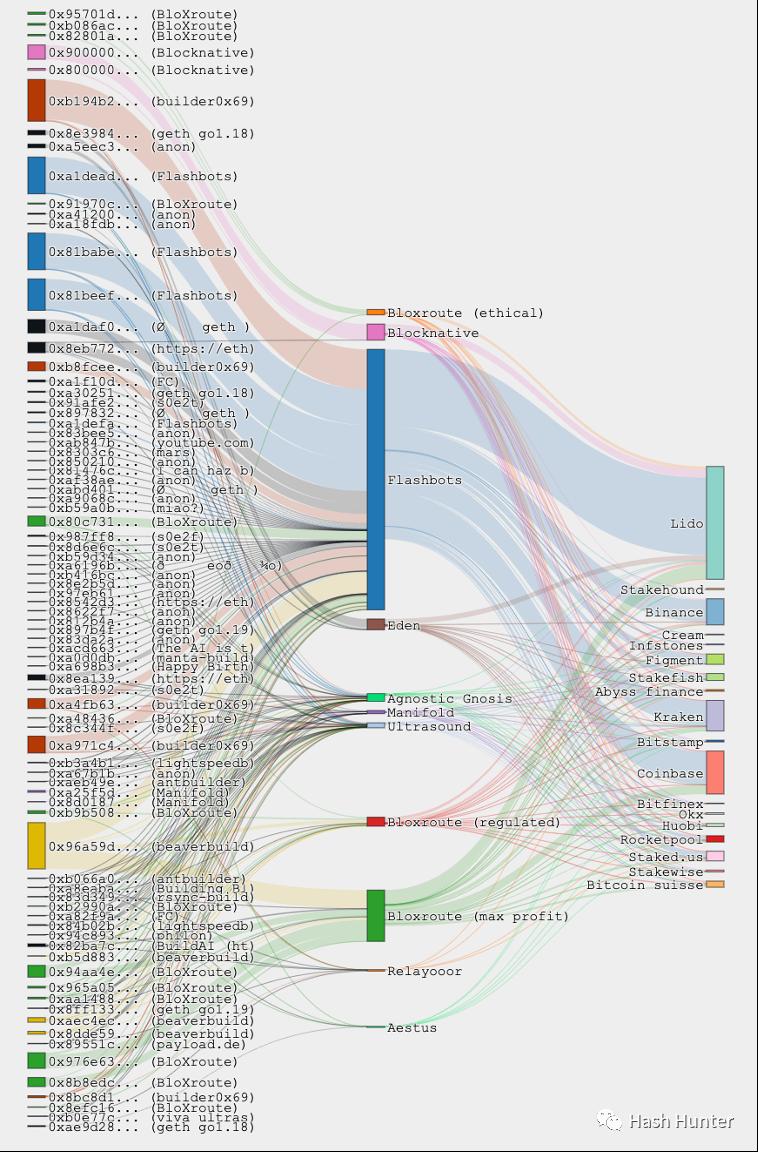
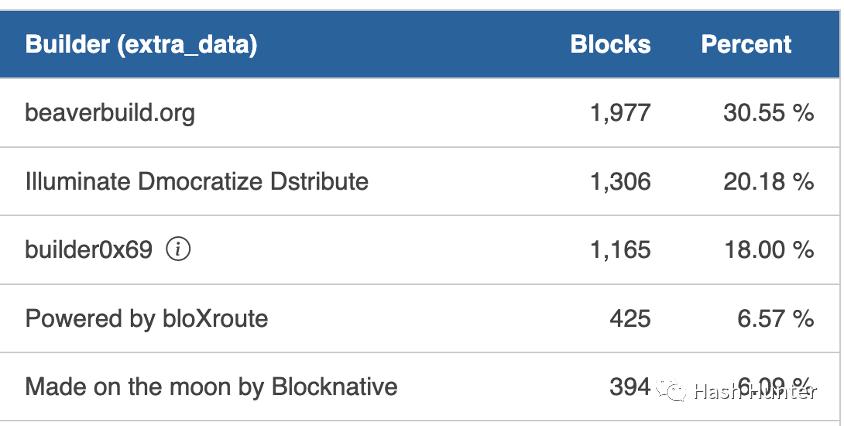
For example: BloXroute, Manifold, Blocknative, Beaverbuild, 0x69, Eden Network, Lightspeed, ETH-Builder, etc. The leftmost part of the image shows the block share of builders, the middle shows the share of relayers, and the right shows the share of validators. Flashbots is not the largest block builder but is currently the largest relayer service provider. In December 2022, I compiled data from 600,000 blocks since the merge.
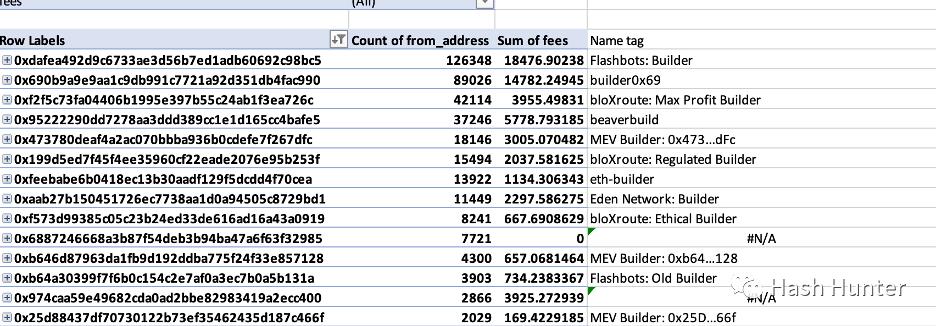
Among them, the market share of the block builder 0x69 is gradually rising and trending to surpass Flashbots. It should be noted that block share does not represent the profit of those blocks. The MEV income paid to validators is determined by block builders, meaning builders can quickly gain validators' favor through subsidies. These projects also provide relayer services, with Flashbots being the largest market share holder among relayers. Currently, there is no data on relayers generating profits. Ultrasound and Agnostic are the only two relayers that do not run their own block building services.
In this field, BloXroute, Manifold, Blocknative, and Eden Network are among the few projects that have publicly raised funds. Eden Network and Manifold only provide block building and relayer services, while BloXroute and Blocknative offer additional services alongside block building. BloXroute provides different relayer interfaces based on validators' needs, such as maximizing profit relayers and regular relayers. Functionally, BloXroute is closer to validator users and project parties, offering node protection services and faster transaction initiation services. Blocknative, on the other hand, is more focused on searchers and some DeFi project parties, providing mempool and transaction simulation services.
Market Size
We can estimate the market size by calculating the future block production volume. The current profit for each block built by existing block builders is approximately 0.0005 Ether. Ethereum produces about 7,000 blocks on average per day. Therefore, the overall block building profit in Ethereum will be around 1,200 Ether, which is actually very low (the overall revenue from the execution layer is around 250,000 Ether). This is also why these project parties have other businesses for income.
Many factors influence block building profits, and current data may not represent the future. For example, block builders may actively lower profits to seize market share, or insufficient transaction volume may affect the number of bundles, etc. From the overall interest chain perspective, the revenue of block builders is more controllable. Their technical architecture also has the potential for large-scale deployment and operation. For project parties, additional paid services can be added based on block building services, making block building and relayer services an attractive option for developers and protocol layer traffic (similar to Web3 infrastructure providing free node calls).
SAAS Services: There are also some business models in the market that provide services to searchers and researchers, such as MEV data analysis by EigenPhi and the mempool data service mentioned above by Blocknative. Another type involves faster private node calling services and node obfuscation services, allowing searchers to conduct node calls and communications discreetly and quickly.
Anti-MEV Services: Currently, there are also some decentralized exchanges that provide anti-frontrunning and sandwich attack services, such as private trading services offered by 1inch and cowswap. Their principle is similar to private RPC services, sending the user's transaction directly to the block builder, ensuring that this transaction does not go through the mempool.
Order Feedback Services: This model is more common in traditional securities markets. Robinhood utilizes this service to generate profits; when retail investors place orders through its software, Robinhood hands over these orders to market makers, who pay Robinhood cash when trading in the market. On-chain transactions can also follow this principle, such as the rook protocol. Users can place orders on the rook-exclusive decentralized exchange, but this transaction will not be executed directly on-chain; instead, it is auctioned internally to rook's keepers.
Once the bidding is successful, the keeper has the authority to include the user's transaction in their bundle, using the user's transaction for MEV activities and profiting. After this transaction concludes, the user receives a portion of rook tokens from the auction, while the keeper gains the MEV profit. In this process, the keeper essentially acts as a searcher, but their order source is no longer the past mempool but rather the private dark pool established by the rook protocol. From the perspective of value distribution, users can obtain a portion of MEV revenue while completing their orders.
Crypto Dark Pool Services: I have also conceived a business model where a new decentralized protocol can establish a protocol-exclusive block building layer and relayer layer while providing trading services. All transactions generated by users using this protocol will enter this dark pool. Searchers need to pay fees to gain exclusive order flow for arbitrage. The protocol layer can return the fees paid by searchers to users, such as through airdrops and gas-free services, thereby attracting more users to engage in dark pool trading.
a. Example: A wallet provider can set up a dedicated dark pool node, ensuring that all transfers and transactions using that wallet are executed through this dark pool: User A exchanges token A for token B on Sushiswap; User B exchanges token B for token A on Uniswap. The moment these two orders combine, it will cause an imbalance in the A-B exchange rate between Uni and Sushi.
Arbitrageurs can auction these two orders and bundle their arbitrage strategies to achieve flash loan arbitrage, etc. Of course, these two transactions must reach a certain scale to realize the exchange imbalance between different pools. Only when the transaction scale reaches a certain level can it be achieved, such as market makers auctioning down 20 user orders to complete a massive arbitrage. Of course, this model also carries significant risks, such as users' transaction losses and excessive centralization of block builders.
SUAVE: By establishing an independent mempool and block construction network, future order flows and blocks can be publicly bid on and accessed by searchers and validators across multi-chain architectures.
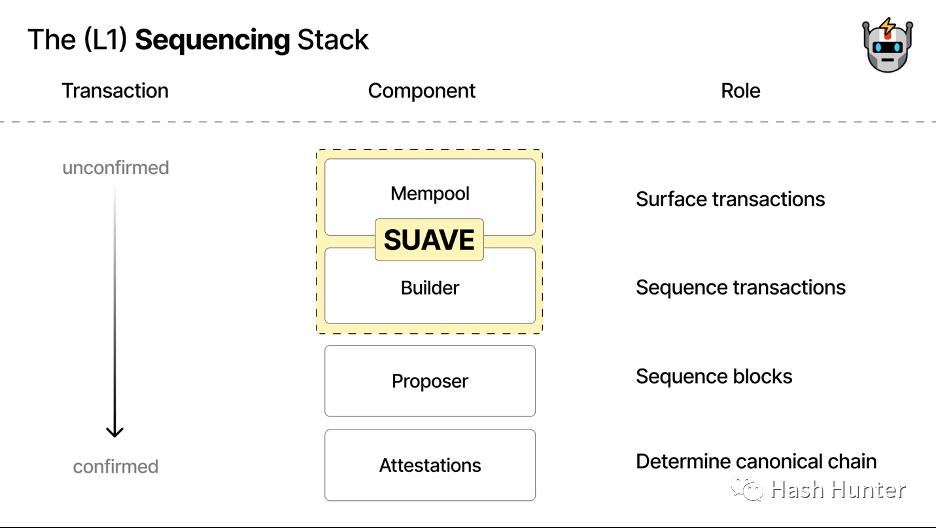
Currently, the architectural design of SUAVE is still in the discussion stage. I believe SUAVE is very likely to launch its dedicated node client. If the existing PBS design is followed, to achieve communication with L2 layers, it must add communication with L2 nodes on top of the existing architecture. This means verifying transaction messages by deploying multiple chain nodes, which is overly cumbersome and complex. It would be better to develop a lightweight node client compatible with all EVM ecosystems to achieve the modular functions described in its documentation.
From the perspective of overall interest distribution, most of the current MEV profits are given to searchers and node validators. Users are often victims rather than beneficiaries. From an investment perspective, anti-MEV and order flow trading are likely to be relatively reliable and high-certainty business models in the future. On one hand, they can attract more ordinary users to participate by utilizing the profits captured from MEV; on the other hand, they can allow searchers to amplify the value of order flow.
Undoubtedly, Flashbots is the leading player in this field, with most of the architectural design and code being open-sourced by them, leading the direction of the entire industry. I believe the opportunities in this field do not lie in arbitrage and staking but in who can possess the ability to build blocks and allocate transactions.
The value of this ability lies not in the economic layer but in the power layer of the entire Ethereum ecosystem—whoever controls the ordering of transactions within blocks controls the distribution of power, and whoever controls the distribution of power can reshape the overall value distribution of the network. In the past, the circulation value of user tokens was distributed through smart contracts and individual transactions, while the future value will be distributed through block builders that combine these order flows. In other words, we will transition from an era of competing for individual transaction values to an era of competing for block space resources.
3. Future Outlook and Concerns
In the era of classical physics, people's understanding of things was continuous. We walk from point A to point B, inevitably experiencing countless intermediate moments; time is continuous, and distance changes are also continuous. It wasn't until Max Planck proposed the hypothesis of energy being discontinuous and divisible in his 1901 paper "On the Normal Distribution of Energy in Normal Spectra" that the iceberg of quantum mechanics was unveiled.
Many users find it difficult to understand MEV because, from our human perspective, we assume that the order we send out can be executed simultaneously in chronological order, which is continuous. From the perspective of the block network, the user's intent and actions are arranged in a series of indivisible orders, which are discontinuous.
Searchers can capture a transaction after the user sends it and reorder it to gain profits. On a macro level, we can approximate that searchers achieve the ability to manipulate time within a small range through bundles. To give an inappropriate example, from the user's perspective, their transaction being subjected to a sandwich attack is akin to being frontrun simultaneously by searchers from the future and the past. The cases discussed in this article all occur on the Ethereum chain, but one thing I can be sure of is that as long as the orders contained within blocks remain non-continuous and indivisible, MEV will inevitably occur.
Centralization Trend:
The power of block building will have profound implications for future protocol layers. As stated in "1984": "Who controls the past controls the future; who controls the present controls the past." From January 3 to 27, over 80% of blocks were created by just 5 block builders.
It is worth mentioning that there is a special function in block building clients where builders can blacklist certain addresses to exclude them from being included in the block. This means that in the future, builders will have the ability to censor transactions. When certain users who do not meet their criteria initiate transactions, those transactions will remain in a pending state and will never reach the real network.
The Tornado-Cash incident was a node-level censorship initiated by major node service providers, while builders initiated mempool-level censorship. Of course, as more users and project parties participate, the decentralization of block building in the future will dilute the impact of such censorship. However, the potential dangers posed by the centralization of block building should not be underestimated. I have conceived several possibilities for readers to consider.
Enforcer Blocks: Suppose that in the future, most builders and node service providers are controlled by a single entity; we will officially enter a blockchain network manipulated by entity laws. Here, all transactions (smart contracts, transfers, authorizations, interactions) will undergo multiple reviews and approvals. Node callers will audit the wallet addresses and IPs of transaction initiators, and once confirmed, the initiated transactions will enter a monitored non-public mempool, where searchers will assume enforcement functions to determine the legality of these transaction contents.
Based on the content and information of the transactions, they will be graded and tagged, then included in bundles and sent to different builders. Builders can place different levels of transactions into blocks with different priorities based on transaction types and functions, which will then be broadcast for validators to review. Transactions that do not comply with entity rules will be discarded in the mempool, preventing any searchers or builders from retrieving them until the user cancels them. In this scenario, hacking and theft activities will be minimized, but users will lose maximum access to the blockchain network, stifling innovation and expression of information.
Enterprise-Level Blocks: Suppose that in the future, builders and node providers are monopolized by a few commercial giants; we will enter a zero-sum game era for block resources. Users and developers may gain relative freedom, but they will be constrained by multiple giant protocols, unable to flexibly choose transaction targets. Even the order flow of users may be auctioned in dark pools at marked prices, leading to exploitation and utilization. We will face the maximum degree of malicious commercial competition, such as builders selling censorship and construction rights for profit. Certain protocols may buy out competitors' order flows, causing delays and disruptions in their users' transactions.
For example, when a user buys and sells on an NFT exchange, when they place an order, that transaction may be placed at the very end of the block by the opposing party, allowing the opposing party's users to snatch up the NFT first, causing the original user's transaction to fail. DEX protocols can also reach agreements with builders to place all opposing transactions into one block, causing temporary token pool imbalances and invalidating the opposing users' transactions. In this scenario, commercial activities still exist, but users and developers must choose sides according to the rules, stifling commercial innovation.
Tampering with History: In cases of excessive concentration of builders and nodes, proof-of-stake chains can delete unwanted past blocks through reorganization attacks. Proof-of-work chains can alter timelines through time thief attacks to re-mine blocks.
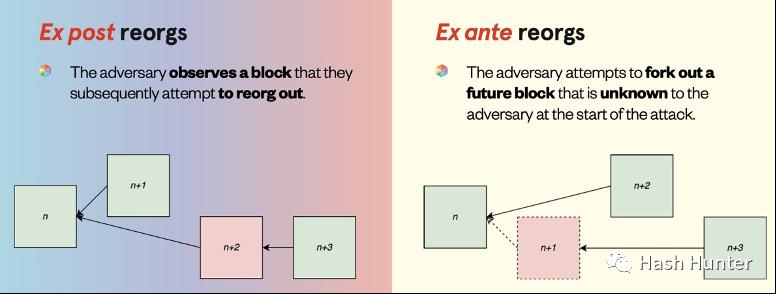
In this scenario, the power machine has the ability to change the past, thereby deleting histories that are unfavorable to them.
Distorting Reality: Current transactions on blockchain networks are concentrated on transfers, contract deployments, and token trading, without having a real impact on the real world. Suppose a product emerges in the future that integrates IoT devices with blockchain networks; then, manipulating orders could interfere with the parameter settings of certain devices in the real world, affecting people's lives. A similar incident has already occurred in the traditional cybersecurity industry: the Colonial Pipeline ransomware incident in May 2021 indirectly led to jet fuel shortages for several airlines in North America.
Illuminating the Dark Forest
The above cases are events that would only occur under very extreme circumstances. The subsequent launch of the SUAVE architecture and…