Analysis of the Incident of Cambodia's Huibang Group Having 29.62 Million USDT Frozen by Teda
Author: Bitrace
Tether USD (USDT) is a centralized stablecoin issued by Tether, which is constrained by smart contracts on the blockchain network and pegged to the value of the US dollar. In addition to the anonymous transfer and permissionless use characteristics of other cryptocurrencies, USDT also grants the issuer significant operational authority, allowing developers to selectively mint or burn USDT tokens for a specific address, or restrict certain addresses' operational permissions on USDT, commonly referred to in the industry as "Tether freezing."
Such centralized freezing activities are usually triggered by law enforcement requests from governments around the world or temporary major cryptocurrency security incidents, aimed at preventing known illegal activities utilizing USDT and intercepting compromised assets to prevent further damage. As the adoption of USDT in the real financial system increases, incidents of illegal activities involving the currency have become more frequent, leading to more common Tether freezing activities, which have had a significant negative impact on many legitimate web3 businesses that inadvertently received risky cryptocurrency funds, even bringing legal risks.
This article will analyze the case of the Cambodian Huione Group being frozen 29.62 million USDT by Tether.
Overview of Huione's Business Scale
Huione Group is a large financial group located in Cambodia, with business segments including cryptocurrency wallets, payments, transaction guarantees, insurance, and cryptocurrency exchanges. Its core payment and guarantee business heavily utilizes USDT. According to the address marking data from Bitrace's DeTrust on-chain risk fund monitoring and management platform, the official and user addresses of HuionePay and HuioneGuarantee exceed 180,000, making it the largest cryptocurrency enterprise in the region, with influence extending throughout Southeast Asia and even East Asia.
 According to Bitrace monitoring, from June 2022 to June 2024, the monthly fund scale of all known HuionePay and HuioneGuarantee business addresses has consistently shown an upward trend, rising from a low of 1.03 billion USDT in June 2022 to a peak of 8.39 billion USDT in April 2024, with a total fund scale reaching 10.2397 billion USDT over the two years.
According to Bitrace monitoring, from June 2022 to June 2024, the monthly fund scale of all known HuionePay and HuioneGuarantee business addresses has consistently shown an upward trend, rising from a low of 1.03 billion USDT in June 2022 to a peak of 8.39 billion USDT in April 2024, with a total fund scale reaching 10.2397 billion USDT over the two years.
 During this period, Huione's related business addresses have also maintained a significant amount of reserves. From June 2022 to June 2024, the average daily balance of all known HuionePay and HuioneGuarantee business addresses reached 35.68 million USDT.
During this period, Huione's related business addresses have also maintained a significant amount of reserves. From June 2022 to June 2024, the average daily balance of all known HuionePay and HuioneGuarantee business addresses reached 35.68 million USDT.
 Due to the high incidence of illegal activities using cryptocurrencies in Southeast Asia, Huione's business addresses have been affected to some extent. Taking the core business address TL8TBp used by HuioneGuarantee as an example, Bitrace monitoring shows that from July 1, 2023, to June 30, 2024, this address received a total of 2.158 billion USDT, of which high-risk funds from online gambling amounted to 35 million, accounting for 1.62%, high-risk funds from black and gray market transactions amounted to 339 million, accounting for 15.71%, high-risk funds from money laundering amounted to 54 million, accounting for 2.50%, and high-risk funds from fraud amounted to 2 million, accounting for 0.09%.
Due to the high incidence of illegal activities using cryptocurrencies in Southeast Asia, Huione's business addresses have been affected to some extent. Taking the core business address TL8TBp used by HuioneGuarantee as an example, Bitrace monitoring shows that from July 1, 2023, to June 30, 2024, this address received a total of 2.158 billion USDT, of which high-risk funds from online gambling amounted to 35 million, accounting for 1.62%, high-risk funds from black and gray market transactions amounted to 339 million, accounting for 15.71%, high-risk funds from money laundering amounted to 54 million, accounting for 2.50%, and high-risk funds from fraud amounted to 2 million, accounting for 0.09%.
Analysis of Frozen Funds at Huione
On July 13, 2024, Tronscan showed that the TRON network address TNVaKW was restricted by Tether, with as much as 29.62 million USDT frozen and unable to be transferred. Bitrace immediately intervened to investigate.

Preliminary investigation results indicated that just five days after its creation, the total transaction scale of TNVaKW exceeded 1 billion USDT, receiving deposits from numerous addresses marked as HuionePayUser on the TRON network, as well as funds from other official HuionePay and HuioneGuarantee addresses. Therefore, Bitrace confirmed that this address is an official business address of Huione and determined that the reason for the freeze was the receipt of a large amount of stolen cryptocurrency funds.
The next day, well-known on-chain detective ZachXBT further stated on social media that assets stolen in the earlier DMM exchange hack in Japan had entered HuionePay through cross-chain exchanges.

Based on the addresses disclosed by ZachXBT, Bitrace uncovered more addresses related to laundering activities and reviewed the entire fund flow. Among them------
\< > 165 BTC was cross-chained to Avalanche via Avalanche Bridge
\< > 182 BTC was cross-chained to Ethereum via ThorChain Bridge
\< > 263 BTC was cross-chained to Ethereum via Threshold Bridge The obtained tBTC, BTC.b, and other assets were exchanged on Avalanche, Ethereum, and other chains for assets equivalent to 31.82 million USD in USDT, USDC, DAI, etc., and then cross-chained to the TRON network, with approximately 14 million eventually entering TNVaKW.

It is worth noting that DMM is just one of the publicly known security incidents involving funds flowing into Huione addresses. During the investigation of other incidents, we found that some funds from the Poloniex exchange hack were also related to Huione. Between June 5 and 7, 2024, at least 1.05 million involved USDT flowed into HuionePay user addresses, subsequently entering multiple official HuionePay business addresses including TLmktr, TR5F41, and TNVaKW.
Currently, there is no direct evidence linking the freezing of TNVaKW to the funds from these two security incidents, but considering that other business addresses of Huione have not been frozen, this at least indicates that this freezing action is not directed at the Huione Group itself.
Analysis of Huione's Payment Run on the Bank
As mentioned earlier, the average daily balance of all known HuionePay and HuioneGuarantee business addresses is 35.68 million USDT, while in the three months prior to the freezing event, this figure had consistently remained around 40 million USDT. The frozen 29.63 million USDT accounts for 75% of its reserves, indicating a certain withdrawal pressure.
Analyzing the latest HuionePay business address TQuFSv------
This address was activated 2.5 hours after TNVaKW was frozen, starting to process deposit and withdrawal requests from HuionePay users, and received an inheritance of 114,800 USDC from TNVaKW. As of 2024/7/16 9:34:39, its transaction scale had reached 733 million USDT.
 Statistics of TQuFSv's income and expenditure on an hourly basis did not reveal any significant abnormal fund movements, and the address currently still holds a balance of 12.88 million USDT.
Statistics of TQuFSv's income and expenditure on an hourly basis did not reveal any significant abnormal fund movements, and the address currently still holds a balance of 12.88 million USDT.
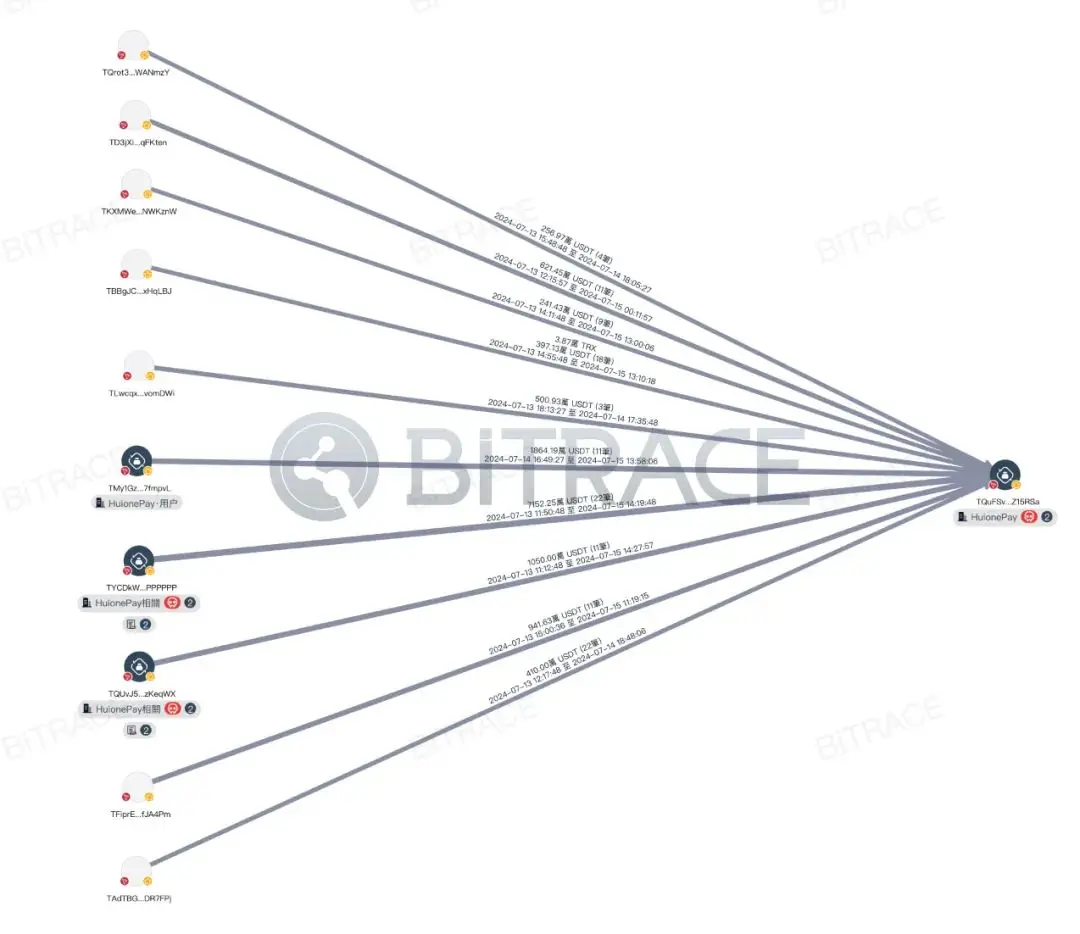
Analyzing the counterparties of TQuFSv, the top ten counterparties by fund inflow transferred a total of 147 million USDT, of which two addresses were marked as HuioneGuarantee addresses, transferring 73 million USDT and 15 million USDT to TQuFSv, accounting for 23.64% of total inflows; the top ten counterparties by fund outflow received a total of 80 million USDT from TQuFSv, of which three addresses were marked as HuioneGuarantee addresses, receiving 14 million USDT, 8 million USDT, and 6 million USDT, accounting for 7.76% of total outflows.
This indicates that after the freezing event, HuionePay experienced a significant outflow of funds, but the official promptly replenished reserves from other business addresses, enabling it to meet users' withdrawal requests.
Importance of KYT
For large-scale enterprises like Huione that adopt cryptocurrencies, sufficient fund throughput often attracts the attention of money laundering groups. Under the increasingly comprehensive law enforcement actions related to cryptocurrency cases globally, a lack of ability to identify the risk of funds from platform user addresses may impact the platform's business and even lead operators into the risk of being investigated.
Therefore, how to use professional KYT tools to accurately identify risky cryptocurrency funds and handle platform risk events based on necessary risk control procedures has become a matter that cryptocurrency-related enterprises must consider.

Based on long-term tracking research on the cryptocurrency crime industry chain, Bitrace has established an exclusive data collection and processing system, building analytical models targeting typical cryptocurrency crime patterns and industry chains. Through machine learning and pattern recognition algorithms, data labeling is dynamically expanded, currently accumulating over 400 million address labels, including entity labels (exchanges, wallets, OTC, payment platforms, mining pools, DeFi, etc.) and exclusive risk labels (money laundering, online gambling, black and gray market, fraud, hacking, sanctions, freezing, terrorism financing, drug trafficking, etc.).
At the same time, the DeTrust on-chain risk fund monitoring and management platform can also help cryptocurrency-related enterprises monitor important business addresses for transactions around the clock, conducting KYT and KYA on every new transaction and counterparty in real-time, supporting customized strategies to achieve dynamic assessment of transaction risks.
Compliance is the foundation of enterprise operation. By establishing appropriate KYT and KYC procedures, enterprises can better meet the requirements of local regulatory authorities and achieve competitive advantages in the market.