Nearly 100 million dollars destroyed: A review of the Nobitex theft incident in Iran
Author: Lisa & 23pds
Editor: Sherry
Background
On June 18, 2025, on-chain detective ZachXBT disclosed that Nobitex, Iran's largest cryptocurrency exchange, was suspected of being hacked, involving abnormal large asset transfers across multiple public chains.

(https://t.me/investigations) SlowMist further confirmed that the affected assets in the incident covered TRON, EVM, and BTC networks, with preliminary estimated losses of about $81.7 million.

(https://x.com/slowmist_team/status/1935246606095593578)
Nobitex also released a statement confirming that some infrastructure and hot wallets had indeed experienced unauthorized access, but emphasized that user funds were safe.

(https://x.com/nobitexmarket/status/1935244739575480472)
It is noteworthy that the attackers not only transferred funds but also actively moved a large amount of assets to specially created burn addresses, with the "burned" assets valued at nearly $100 million.

(https://x.com/GonjeshkeDarand/status/1935412212320891089)
Timeline
June 18
- ZachXBT disclosed that the Iranian cryptocurrency exchange Nobitex was suspected of being hacked, with a large number of suspicious withdrawal transactions occurring on the TRON chain. SlowMist further confirmed that the attack involved multiple chains, with preliminary estimated losses of about $81.7 million.
- Nobitex stated that its technical team detected unauthorized access to some infrastructure and hot wallets, and immediately cut off external interfaces and initiated an investigation. The vast majority of assets stored in cold wallets were unaffected; this intrusion was limited to a portion of hot wallets used for daily liquidity.
- The hacker group Predatory Sparrow (Gonjeshke Darande) claimed responsibility for the attack and announced that they would release Nobitex's source code and internal data within 24 hours.

(https://x.com/GonjeshkeDarand/status/1935231018937536681)
June 19
- Nobitex released its fourth statement, indicating that the platform had completely blocked external access to its servers, and that the hot wallet transfers were "proactive migrations made by the security team to protect funds." At the same time, the official confirmed that the stolen assets were transferred to wallets with non-standard addresses composed of arbitrary characters, which were used to destroy user assets, totaling about $100 million.
The hacker group Predatory Sparrow (Gonjeshke Darande) claimed to have burned approximately $90 million worth of cryptocurrency assets, referring to them as "sanction evasion tools."
The hacker group Predatory Sparrow (Gonjeshke Darande) publicly released Nobitex's source code.

(https://x.com/GonjeshkeDarand/status/1935593397156270534)
Source Code Information
According to the source code information released by the attackers, the folder information is as follows:

Specifically, it involves the following content:

Nobitex's core system is primarily written in Python and uses K8s for deployment and management. Based on known information, we speculate that the attackers may have breached operational boundaries to enter the internal network, which will not be analyzed further here.
MistTrack Analysis
The attackers used multiple seemingly legitimate but actually uncontrollable "burn addresses" to receive assets. Most of these addresses comply with on-chain address format validation rules and can successfully receive assets, but once funds are transferred in, they are effectively permanently destroyed. Additionally, these addresses contain emotional and provocative language, indicating an attack intent. Some of the "burn addresses" used by the attackers are as follows:
- TKFuckiRGCTerroristsNoBiTEXy2r7mNX
- 0xffFFfFFffFFffFfFffFFfFfFfFFFFfFfFFFFDead
- 1FuckiRGCTerroristsNoBiTEXXXaAovLX
- DFuckiRGCTerroristsNoBiTEXXXWLW65t
- FuckiRGCTerroristsNoBiTEXXXXXXXXXXXXXXXXXXX
- UQABFuckIRGCTerroristsNOBITEX1111111111111111_jT
- one19fuckterr0rfuckterr0rfuckterr0rxn7kj7u
- rFuckiRGCTerroristsNoBiTEXypBrmUM
We used the on-chain anti-money laundering and tracking tool MistTrack for analysis, and Nobitex's losses are partially summarized as follows:
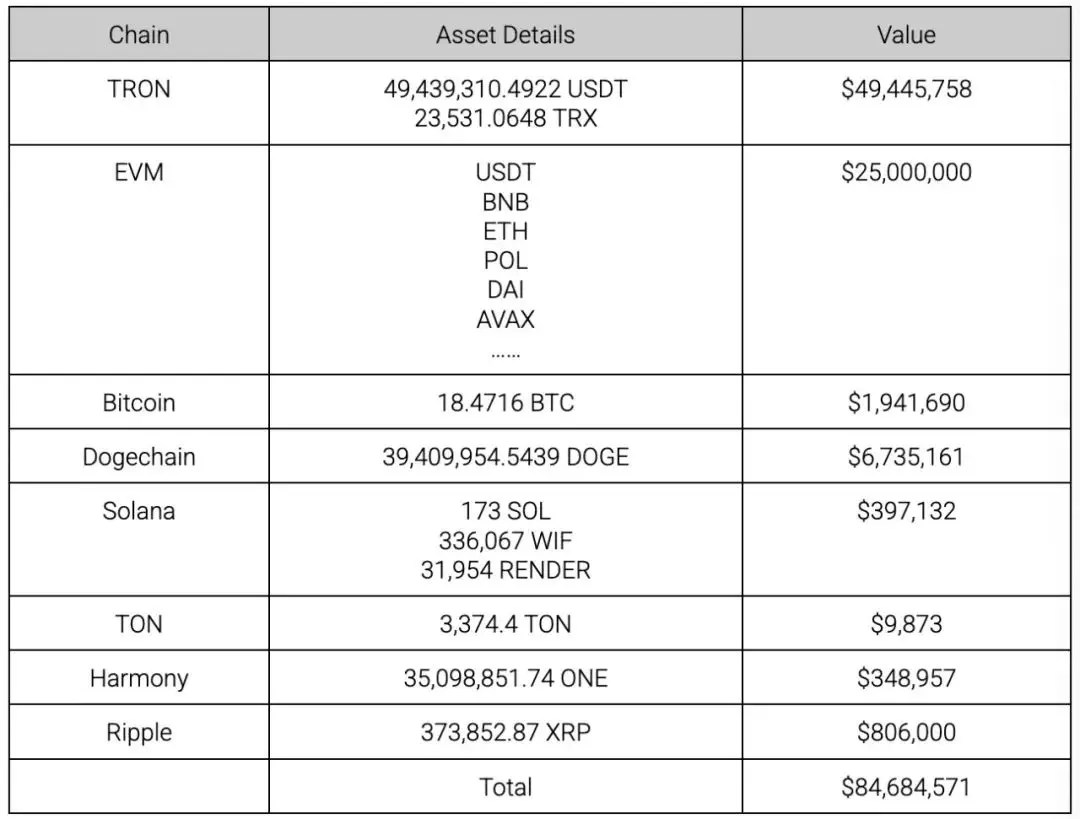
According to MistTrack analysis, the attackers completed 110,641 USDT transactions and 2,889 TRX transactions on TRON:

The assets stolen by the attackers on EVM chains mainly include BSC, Ethereum, Arbitrum, Polygon, and Avalanche, covering not only mainstream coins in each ecosystem but also various tokens such as UNI, LINK, and SHIB.

On Bitcoin, the attackers stole a total of 18.4716 BTC, approximately 2,086 transactions.

On Dogechain, the attackers stole a total of 39,409,954.5439 DOGE, approximately 34,081 transactions.

On Solana, the attackers stole SOL, WIF, and RENDER:

On TON, Harmony, and Ripple, the attackers stole 3,374.4 TON, 35,098,851.74 ONE, and 373,852.87 XRP, respectively:

MistTrack has added the relevant addresses to the malicious address database and will continue to monitor related on-chain movements.
Conclusion
The Nobitex incident serves as a reminder to the industry: security is a whole, and platforms need to further strengthen security protections, adopting more advanced defense mechanisms, especially for platforms that use hot wallets for daily operations. SlowMist recommends:
- Strictly isolate the permissions and access paths of hot and cold wallets, and regularly audit hot wallet access permissions;
- Use on-chain real-time monitoring systems (such as MistEye) to obtain comprehensive threat intelligence and dynamic security monitoring in a timely manner;
Collaborate with on-chain anti-money laundering systems (such as MistTrack) to promptly detect abnormal fund flows;
Strengthen emergency response mechanisms to ensure effective responses within the golden window after an attack occurs.
The investigation into the incident is still ongoing, and the SlowMist security team will continue to follow up and provide timely updates on the progress.