How did XPL attackers leverage Hyperliquid's rules to teach all DEX a lesson worth tens of millions of dollars?
Author: Carrot
This is not hacking, it's a conspiracy
A couple of days ago, a textbook-level "precision strike" took place on Hyperliquid, with the protagonist being a token called $XPL. In the end, the attacker managed to orchestrate a large-scale short liquidation with a cost of less than $200,000, profiting over ten million dollars.
The key point is: this was not a hacking attack; the attacker did not exploit any code vulnerabilities.
On the contrary, what he utilized was the DEX's proud feature—complete transparency. This was a hunt conducted in broad daylight, fully compliant with the protocol rules. This incident serves as a mirror, reflecting the structural weaknesses hidden beneath the shiny exterior of all current on-chain exchanges (DEX).
Part One: The Trilogy of Attack: How Did the Hunt Happen?
To understand this attack, you first need to know a core mechanism of perpetual contract exchanges: the Price Feed. Simply put, contract platforms need a "real price" to determine who profits, who loses, and who should be liquidated. This "real price" usually comes from external sources, such as the on-chain spot market.
The attacker's script revolves around this "Price Feed" mechanism in a trilogy:
Step One: Finding the Perfect Prey
The attacker found $XPL. The perfection of this token lies in the fact that its perpetual contracts have trading volume on Hyperliquid, but its spot trading is almost entirely concentrated in a small exchange called Zebra on the Arbitrum chain, with extremely shallow liquidity. This means that with very little money, the spot price can be driven sky-high.
Step Two: Polluting the Price Source
According to on-chain data, the attacker spent about $184,000 in WETH to frantically buy XPL spot on Zebra. The result was immediate, with the spot price being driven up nearly 8 times in a short period. Hyperliquid's price feed mechanism referenced this spot price, thus the "real price" in the contract was successfully polluted, artificially pushed to an absurd height.
Step Three: Harvesting the Short Army
When the contract price soared abnormally, all short positions were forced to face liquidation. On a completely transparent order book platform like Hyperliquid, who would be liquidated at what price is almost a semi-public secret. The attacker watched this "liquidation map" and precisely pushed the price past the trigger point. A large number of shorts were forcibly liquidated, while the attacker, who had already set up an ambush, easily took these blood-stained chips, ultimately profiting about 15 million dollars.


Part Two: Is the DEX's "Complete Transparency" a Blessing or a Curse?
This incident raises a soul-searching question: Is the transparency that DEX prides itself on a good thing or a curse?
It is a sharp double-edged sword.
For ordinary users, transparency means fairness, verifiability, and no behind-the-scenes manipulation. But in the eyes of the attacker, a transparent order book is an attack map, and automated smart contracts are executioners.
The protocol is neutral; it cannot distinguish between good and evil. As long as you play by the rules, it executes faithfully. This "absolute neutrality" becomes a cash machine for whales in the face of low liquidity markets. This is why, in the face of such naked attacks, the protocol itself is powerless.
Part Three: So, is it safe to retreat back to CEX?
Since DEX is so dangerous, how about returning to the embrace of CEX?
CEX does have its "firewalls." Strict KYC, internal risk control teams, and price limit mechanisms can effectively increase the difficulty of such attacks. Trying to manipulate a token's contract price with $200,000 on Binance is almost a pipe dream.
But is it safe? No. CEX merely transforms the risk from "transparent evil" to "invisible evil."
On DEX, the rules are public, and the risks are calculable. In CEX, you face a black box. Your greatest risk is no longer external snipers but the exchange itself. The stories of FTX and Alameda Research are the best proof—when self-dealing occurs, you will know nothing until everything goes to zero.
Therefore, the key issue has never been which is better, DEX or CEX, but how to learn from both and create a more evolved species.

Part Four: Seeking Answers from the Architectural Foundation—Taking QuBitDEX as an Example
The $XPL incident tells us that merely moving trading on-chain is far from enough. The future of the industry must address these fundamental issues from an architectural level.
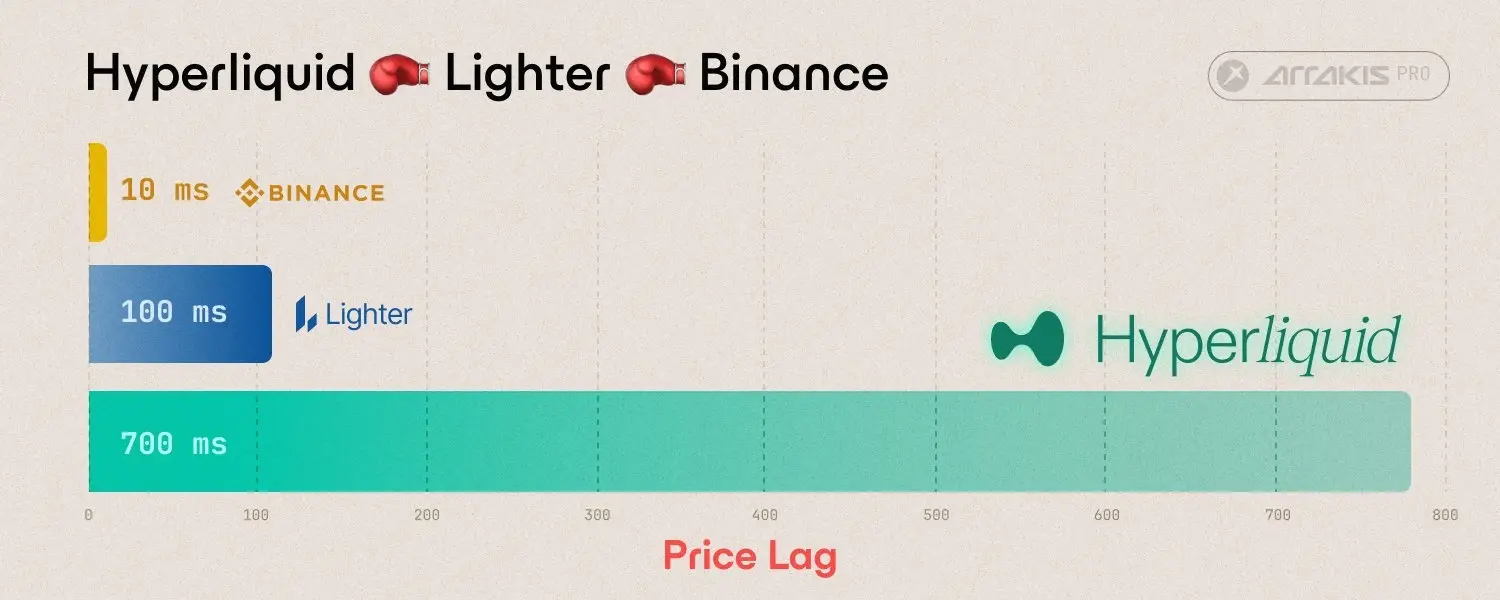
First, the price feed mechanism must evolve. A single, low-liquidity spot market can never be the sole basis for determining the life and death of tens of millions of dollars in positions. For example, QuBitDEX has been exploring and establishing one of its core principles since its inception: by aggregating depth data streams from multiple leading CEXs and combining them with a time-weighted average price (TWAP) mechanism, it fundamentally raises the cost of price pollution exponentially.
Second, absolute transparency needs to be rethought. Is there a possibility to ensure the verifiability of settlements while protecting traders' strategic privacy? This is also the direction QuBitDEX is exploring through its native Layer-1 ZK compatibility. Hybrid trading models like on-chain dark pools can effectively prevent malicious sniping without sacrificing the foundational trust of decentralization.
Finally, the protocol itself must become "smarter." It needs to possess native risk management capabilities, rather than being just a passive executor. The architecture described in the QuBitDEX white paper features a native AI layer designed as a real-time risk engine capable of dynamically analyzing the market, identifying abnormal trading patterns, and providing a basis for protocol-level risk control. This approach of embedding risk management into the protocol's DNA represents an important evolutionary direction for DEX architecture.
Final Conclusion
The XPL incident has taught everyone a lesson worth millions of dollars: the next generation of DEX cannot simply be a straightforward on-chain replica. The future of the industry belongs to those protocols that can deeply understand and address these structural vulnerabilities.
True innovation comes from platforms that can deeply synthesize the mature risk control concepts of CEX with the verifiable and decentralized spirit of DEX.